Category | CLOUD and AWS
Last Updated On 09/03/2026
Many cloud networking problems begin with the same mistake—launching resources directly into the cloud without proper network isolation. Applications become exposed, traffic flows unpredictably, and security becomes harder to manage. This is exactly why Amazon VPC plays such an important role in AWS architecture.
If you’re learning cloud networking, the first concept you will encounter is What is Amazon VPC and how it helps organizations design secure and scalable cloud networks. Amazon VPC (Virtual Private Cloud) allows you to create a logically isolated network inside AWS where you can launch resources like EC2 instances, databases, and application services.
Instead of relying on shared public networks, teams can control their own IP address ranges, routing rules, and security policies. In this article, we will break down Amazon VPC architecture, explain the key components, and show how cloud applications run inside a properly designed VPC environment.
Topic |
Key Insight |
|---|---|
What is Amazon VPC |
A private virtual network inside AWS for launching resources securel |
Core networking component |
CIDR blocks, subnets, route tables, gateways |
Security controls |
Security Groups and Network ACLs |
Connectivity options |
VPC Peering, VPN, Direct Connect, PrivateLink |
Typical architecture |
Public subnets for web servers, private subnets for databases |
Typical architecture |
Public subnets for web servers, private subnets for databases |
With this overview in mind, let’s look deeper into What is Amazon VPC and why it forms the foundation of AWS networking.
To understand AWS networking, it is important to clearly answer What is Amazon VPC.
Amazon VPC is a virtual network dedicated to your AWS account. It allows organizations to create isolated cloud environments where applications and infrastructure resources can run securely.
Inside a VPC, you control:
IP address ranges
Subnet design
Routing policies
Network security rules
Connectivity with external networks
This level of control makes Amazon VPC similar to designing your own data center network—but inside the AWS cloud.
Default vs Custom VPC
Every AWS account includes a default Amazon VPC. The default VPC allows users to quickly launch resources without manually configuring networking.
However, most organizations prefer creating custom Amazon VPC environments because they allow:
Stronger security policies
Better network segmentation
High availability architectures
Custom routing configurations
Understanding What is Amazon VPC becomes easier when you see it as the networking foundation that supports every application running in AWS.
In cloud architecture workshops, learners typically create custom VPC environments using segmented CIDR ranges. This approach helps teams design scalable multi-tier architectures supporting hundreds of compute instances across multiple Availability Zones.
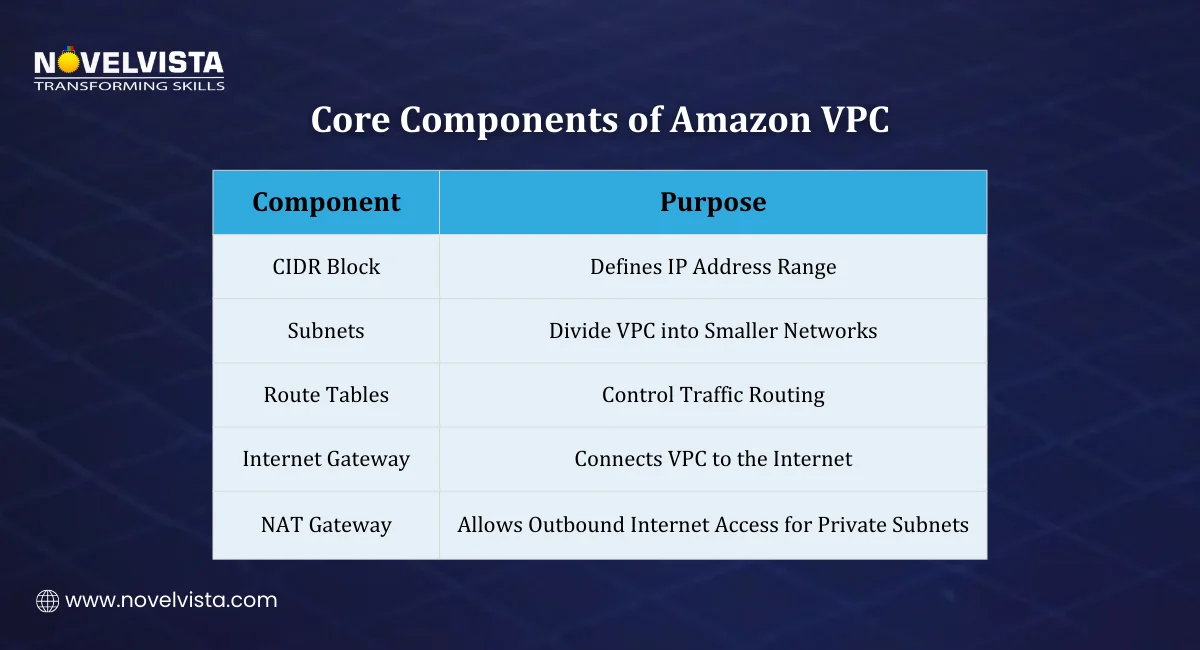
To design cloud networks properly, we must understand what are the components of an Amazon VPC.
A VPC is built using several networking components that define how resources communicate with each other and with external networks.
Below are the most important elements of Amazon VPC architecture.
1. CIDR Block
The CIDR block defines the IP address range for the VPC.
For example:
10.0.0.0/16
This range determines how many private IP addresses can exist inside the VPC.
Key points:
Supports IPv4 and IPv6 addressing
CIDR sizes range from /28 (smallest) to /16 (largest)
Defines the maximum number of resources in the VPC
Every Amazon VPC must have at least one CIDR block.
2. Subnets
Subnets divide a VPC into smaller networks. They are created inside specific Availability Zones (AZs) to support high availability.
Two common subnet types exist.
A. Public Subnets
Public subnets contain resources that must be accessible from the internet.
Examples include:
Web servers
Load balancers
Bastion hosts
These subnets connect to the internet using an Internet Gateway.
B. Private Subnets
Private subnets host internal services that should not be exposed to the internet.
Examples include:
Application servers
Databases
Internal APIs
Private subnets improve security by limiting external access. These subnet designs are central when discussing What are the components of an Amazon VPC.
3. Route Tables
Route tables control how network traffic flows within Amazon VPC. Each subnet must be associated with a route table. Routes define how traffic moves to different destinations. Common route targets include:
Local routing within the VPC
Internet Gateway (IGW)
NAT Gateway
VPC endpoints
By defining routes properly, administrators control how data flows across cloud networks.
4. Internet Gateway (IGW)
The Internet Gateway allows resources inside public subnets to communicate with the internet.
It performs two main functions:
Allows inbound internet traffic
Allows outbound internet traffic
Instances in public subnets rely on this gateway to interact with external users.
5. NAT Gateway
Private subnet instances often need internet access for tasks like:
Software updates
Security patches
API calls
However, they should not be directly accessible from the internet. A NAT Gateway solves this problem. It allows:
Outbound internet access from private subnets
Blocking inbound internet connections
This ensures security while maintaining functionality. Understanding What are the components of an Amazon VPC helps architects design reliable cloud networking systems.
Networking alone is not enough—security is equally important. Amazon VPC includes multiple security layers that control traffic access.
Two primary security mechanisms exist.
Security Groups
Security groups act as instance-level firewalls. They control which traffic is allowed to reach resources. Security groups are stateful, meaning:
If inbound traffic is allowed, return traffic is automatically permitted.
Security group rules define:
Allowed protocols
Port ranges
Source or destination IP addresses
Because of this behavior, security groups are commonly used to secure EC2 instances inside Amazon VPC.
Network Access Control Lists (NACLs)
Network ACLs operate at the subnet level. Unlike security groups, they are stateless. This means rules must be defined for:
Inbound traffic
Outbound traffic
NACLs provide an additional layer of security in the Amazon VPC architecture.
During cloud security training exercises, teams frequently test layered controls using both Security Groups and NACLs. This approach helps simulate enterprise environments where multiple network security checkpoints are required.
Once the internal networking components are in place, the next step is understanding how Amazon VPC connects with other networks and services. Most modern cloud architectures require communication between multiple VPCs, on-premise systems, and AWS services.
AWS provides several connectivity options that extend the capabilities of Amazon VPC.
VPC Peering
VPC Peering allows two VPCs to connect directly with each other. Key characteristics include:
Private communication between two VPC networks
Traffic stays within AWS infrastructure
No internet gateway required
However, VPC Peering has one limitation: it is non-transitive. This means traffic cannot automatically pass through one VPC to reach another.
Despite that limitation, VPC Peering is commonly used when applications in separate VPC environments need secure internal communication.
VPN and AWS Direct Connect
Many organizations run hybrid infrastructures that combine on-premise data centers with AWS cloud services. To support this model, Amazon VPC provides two connectivity methods.
Site-to-Site VPN
Connects on-premise networks to AWS using encrypted tunnels
Uses IPsec for secure communication
AWS Direct Connect
Provides a dedicated private connection between on-premise networks and AWS
Offers lower latency and more consistent performance than internet-based connections
These connectivity options help organizations extend their infrastructure into the cloud securely.
VPC Endpoints and PrivateLink
Some applications require access to AWS services without exposing traffic to the public internet. VPC Endpoints and AWS PrivateLink enable private connectivity between Amazon VPC and AWS services.
Benefits include:
Private access to services like S3 and DynamoDB
Improved security by avoiding public internet traffic
Simplified network architecture
These capabilities are particularly useful for applications that must meet strict security or compliance requirements.
AWS Transit Gateway
Large organizations often operate dozens or even hundreds of VPC environments. Managing direct connections between all of them can quickly become complex. AWS Transit Gateway simplifies this architecture.
It acts as a central hub that connects multiple networks, including:
Multiple VPCs
On-premise environments
VPN connections
This centralized model makes large Amazon VPC environments easier to manage.
When designing cloud environments, architects often follow a common Amazon VPC architecture pattern. Most production architectures span multiple Availability Zones (AZs) to ensure reliability and high availability.
A typical architecture includes several layers.
Public Subnet Layer
Public subnets host components that must receive internet traffic. Examples include:
Web servers
Load balancers
Bastion hosts
These resources connect to the internet through an Internet Gateway.
Private Application Layer
Application servers are usually placed inside private subnets. This protects internal application logic from direct internet exposure. These servers typically communicate with public components through internal routing.
Database Layer
Databases are also placed in private subnets. This ensures that sensitive data systems are not directly accessible from external networks.
Common deployments include:
Amazon RDS Multi-AZ databases
Internal data processing services
High Availability Architecture
To ensure reliability, many architectures also include:
Application Load Balancer (ALB) distributing traffic across multiple AZs
Auto Scaling groups automatically adjust compute capacity
Multi-AZ database deployments for redundancy
Traffic within Amazon VPC usually follows this flow:
Router → Route Table → Network ACL → Security Group → Instance
This layered architecture allows organizations to design secure and scalable cloud environments.
In AWS architecture implementation labs, learners frequently deploy multi-tier applications using separate subnet layers. This design pattern mirrors production environments where web, application, and database tiers remain isolated.
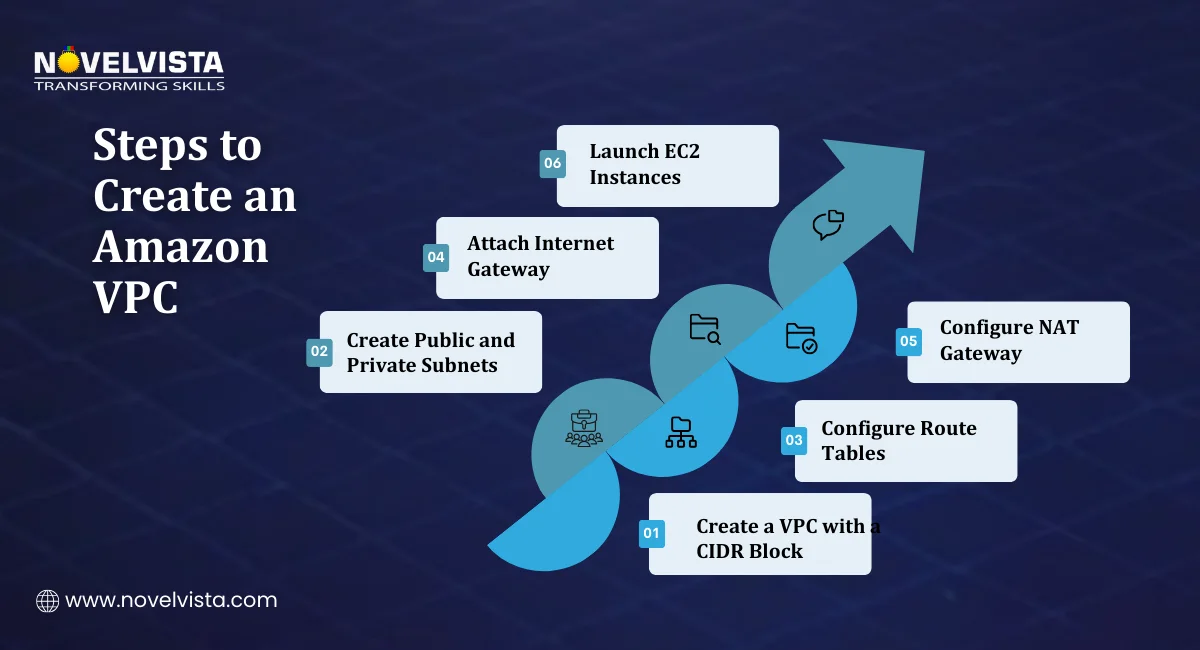
Understanding the deployment process helps explain how cloud networking is actually built. When setting up a VPC environment, administrators typically follow a structured process.
Step 1: Create the VPC
The first step is creating a VPC with a defined CIDR block.
Example:
10.0.0.0/16
This block defines the IP address space available within the Amazon VPC.
Step 2: Create Subnets
Next, subnets are created across multiple Availability Zones. These subnets divide the network into smaller segments.
Typical architectures include:
Public subnets
Private application subnets
Private database subnets
Step 3: Configure Route Tables
Each subnet is associated with a route table. Routes determine where network traffic should be directed.
For example:
Internet traffic → Internet Gateway
Internal traffic → local VPC routing
Step 4: Attach Internet Gateway
To allow internet access, an Internet Gateway must be attached to the VPC. Public subnet instances can then communicate with external networks.
Step 5: Configure NAT Gateway
Private subnets often require outbound internet access. A NAT Gateway enables this while keeping the instances hidden from the public internet.
Once configured, resources inside the same Amazon VPC communicate using private IP addresses.
Connectivity can then be expanded through:
VPC Peering
VPN connections
Private endpoints
Understanding how to use Amazon VPC is essential for designing scalable cloud applications.
A practical cheat sheet explaining VPCs, subnets, route tables, gateways,
and security controls to help you understand core AWS networking concepts quickly.
Organizations typically deploy applications inside VPC environments using structured workflows.
How to use Amazon VPC for application deployment usually follows these steps.
Create a VPC with the desired IP address range
Create public and private subnets
Configure route tables and security groups
Launch EC2 instances inside the defined subnets
Configure load balancers and scaling groups
Enable private endpoints or VPC peering if required
A common deployment architecture looks like this:
Public Subnets
Application Load Balancer
Web servers
Private Subnets
Application servers
Databases
This architecture improves security by isolating critical components from public access.
Industry data highlights how widely this design is used.
There are several reasons why Amazon VPC has become the standard networking solution in AWS.
Network Isolation
Amazon VPC allows organizations to isolate infrastructure from public networks. This improves security and reduces exposure to external threats.
Flexible Network Architecture
Organizations can design custom networking architectures, including:
Multi-tier applications
Hybrid cloud connectivity
Multi-region deployments
This flexibility makes Amazon VPC suitable for many different workloads.
High Scalability
Amazon VPC supports infrastructure across:
Multiple Availability Zones
Multiple regions
Thousands of resources
This scalability allows organizations to grow cloud infrastructure without major redesign.
Integration with AWS Networking Services
Amazon VPC integrates with several AWS services, including:
Elastic Load Balancing
AWS Transit Gateway
AWS Direct Connect
AWS PrivateLink
These integrations allow teams to build advanced networking architectures. In many cloud certification programs, VPC architecture is a core exam topic. Professionals preparing for AWS architect roles frequently practice designing secure multi-tier VPC environments before certification assessments.
Cloud networking is the foundation of every application running on AWS, and Amazon VPC plays a central role in building secure environments.
By combining CIDR blocks, subnets, routing rules, security layers, and connectivity services, organizations can create highly controlled cloud networks.
Understanding What is Amazon VPC and how its components work together helps architects design reliable, scalable infrastructure.
Next Step: Build Your AWS Architecture Skills
If you want to design secure and scalable cloud infrastructure, NovelVista’s AWS Solution Architect Associate Professional Certification Training can help you build the required skills. The program covers AWS networking, architecture design, security best practices, and real-world cloud deployment strategies. Through practical training and expert guidance, professionals learn how to implement services like Amazon VPC effectively in modern cloud environments.
Author Details
Course Related To This blog
AWS Certified AI Practitioner
AWS MasterClass Series
AWS Certified Cloud Practitioner (CLF-C02)
AWS Certification
AWS Certified Developer Associate
AWS Solution Architect Associates
Confused About Certification?
Get Free Consultation Call
Stay ahead of the curve by tapping into the latest emerging trends and transforming your subscription into a powerful resource. Maximize every feature, unlock exclusive benefits, and ensure you're always one step ahead in your journey to success.