Category | Other
Last Updated On 10/06/2026
You studied hard, got your certification, and now you're sitting in front of an interviewer who asks, "Walk me through how you'd carry out a penetration test." Blank. That moment of panic is more common than you think.
Most candidates prepare theory but forget that interviewers want you to think like an attacker. This guide covers the most important Ethical Hacking Interview Questions across all levels: fresher, intermediate, and advanced, so you walk into that room actually ready.
Section |
Key Takeaway |
|---|---|
Fresher Questions |
Focus on core concepts: hacking types, 5 stages, basic tools |
Intermediate Questions |
Understand real attacks: SQL injection, XSS, DDoS, ARP poisoning |
Advanced Questions |
Know pen testing methodology, CVSS scoring, and exploitation techniques |
Network & Scanning |
Master recon, enumeration, OS fingerprinting, and threat models |
Tips |
Explain both how attacks work AND how to stop them |
If you're just starting out, interviewers aren't expecting you to have hacked a server. They want to know if you understand the foundations. Get these right, and you immediately stand out from other freshers.
1. What is ethical hacking, and how does it differ from malicious hacking?
Ethical hacking is basically doing what a malicious hacker does, but with full permission from the organization. You're finding weaknesses before the bad guys do. The key difference isn't the technique; it's the authorization. A malicious hacker breaks in without permission. An ethical hacker has a signed agreement before touching anything
2. What are the different types of hackers?
3. What are the five stages of hacking?
This one comes up in almost every interview. Learn it cold.
4. Common ethical hacking tools, and what they do:
Tool | Purpose |
|---|---|
| Nmap | Network scanning and port discovery |
| Metasploit | Exploitation framework for testing vulnerabilities |
| Wireshark | Packet capture and network traffic analysis |
An IP address is a logical address that changes depending on the network you're on. A MAC address is a physical address burned into your network card; it stays the same. In security, MAC addresses matter because attacks like MAC spoofing and MAC flooding target this layer directly.
Footprinting is the very first step of any security assessment. Before you can attack or test anything, you need to understand what's out there: domain names, IP ranges, employee details, and technologies in use. It's about building a complete picture of your target before doing anything active.
Encryption is reversible. You can decrypt it with the right key. Hashing is one-way; once data is hashed, you can't reverse it back to the original. Passwords are stored as hashes, not encrypted. If a company tells you they encrypt passwords, that's actually a red flag in security terms.
Dictionary attacks are faster. Brute force takes longer but is more thorough. In practice, attackers combine both.
Once you move past the basics, interviewers start testing whether you actually understand how attacks happen, not just what they're called. These Ethical Hacking Technical Interview Questions will push you to explain both the attack and the defense.
1. What is the difference between active and passive sniffing?
Passive sniffing listens to network traffic without sending anything; it works on hub-based networks where all traffic is visible. Active sniffing involves injecting traffic or using techniques like ARP poisoning to redirect traffic on switched networks. Tools like Wireshark and Tcpdump are used for both.
2. What is ARP poisoning?
ARP (Address Resolution Protocol) links IP addresses to MAC addresses on a local network. In ARP poisoning, the attacker sends fake ARP replies to associate their MAC address with a legitimate IP, so all traffic meant for that IP flows through the attacker first. Prevention includes using dynamic ARP inspection on switches and static ARP entries for critical devices.
3. What is SQL Injection?
SQL injection is when an attacker inserts malicious SQL code into an input field, like a login form, to manipulate the database behind it. For example, entering ' OR '1'='1 can bypass login authentication entirely. The fix? Use parameterized queries (also called prepared statements), which treat user input as data, not code.
4. What is Cross-Site Scripting (XSS)?
XSS happens when an attacker injects malicious scripts into a webpage that other users then load. The three main types:
Stored XSS: The script is saved on the server and runs every time the page loads
Reflected XSS: The script is embedded in a URL and runs immediately when clicked
DOM-based XSS: The attack happens entirely in the browser without server involvement
5. What is a DDoS attack and its three main types?
A Distributed Denial of Service (DDoS) attack floods a target with traffic to make it unavailable. The three types:
Volume-based attacks: Overwhelm bandwidth with sheer traffic volume
Protocol attacks: Exploit weaknesses in network protocols (like SYN floods)
Application-layer attacks: Target specific web applications to exhaust server resources
6. What is MAC flooding?
Switches maintain a table that maps MAC addresses to ports. MAC flooding bombards the switch with thousands of fake MAC addresses until the table is full. Once full, the switch starts behaving like a hub, broadcasting all traffic to all ports, which lets an attacker sniff traffic they shouldn't be able to see.
Senior roles don't just need you to name attacks; they need you to run a full test. These interview questions on ethical hacking are designed to evaluate how you think under real-world conditions.
1. How do you approach a full penetration test?
A professional pen test follows a clear structure:
Reconnaissance: Passive and active information gathering
Scanning & Enumeration: Identifying live hosts, open ports, and running services
Exploitation: Attempting to exploit discovered vulnerabilities
Post-Exploitation: Assessing what an attacker could do once inside
Reporting: Documenting findings, risk ratings, and remediation steps
The final report is just as important as the technical work, it's what the client actually acts on.
2. What is the difference between a vulnerability assessment and a penetration test?
A vulnerability assessment identifies and lists potential weaknesses. A penetration test actually tries to exploit them. VA tells you what might be wrong. PT shows you what an attacker could actually do with those weaknesses.
3. What is CVSS scoring?
CVSS (Common Vulnerability Scoring System) gives vulnerabilities a score from 0 to 10 based on factors like attack complexity, whether authentication is needed, and the impact on confidentiality, integrity, and availability. It's the standard way pen testers prioritize what to fix first.
4. What is Burp Suite?
Burp Suite is a web application testing toolkit used to intercept, inspect, and modify HTTP/HTTPS traffic between a browser and a web server. It's the go-to tool for finding issues like SQL injection, XSS, and broken authentication in web apps.
5. What is a Man-in-the-Middle (MitM) attack?
In a MitM attack, the attacker secretly positions themselves between two communicating parties, intercepting and potentially modifying the data passing between them. ARP poisoning is one common way to set up a MitM on a local network.
Master key cybersecurity concepts, tools, and real-world scenarios with 120 interview questions
covering networking, penetration testing, vulnerabilities, and incident response.
1. What is the difference between active and passive reconnaissance?
Passive recon gathers information without directly interacting with the target, using public sources like WHOIS, LinkedIn, or Google. Active recon involves directly probing the target, like running an Nmap scan. Active recon leaves traces; passive recon doesn't.
2. What is OS fingerprinting?
OS fingerprinting identifies which operating system a target is running based on how it responds to network packets. Tools like Nmap can do this passively or actively. Knowing the OS helps an attacker (or tester) choose the right exploits.
3. What is LDAP enumeration?
LDAP (Lightweight Directory Access Protocol) is used by networks to organize user and resource information. LDAP enumeration can expose usernames, email addresses, department structures, and even password policies, giving an attacker a detailed map of an organization's internal structure.
4. What is the STRIDE threat model?
STRIDE helps security teams think through how a system can be attacked:
Spoofing: Pretending to be someone else
Tampering: Modifying data without authorization
Repudiation: Denying that an action took place
Information Disclosure: Exposing data to unauthorized users
Denial of Service: Making a system unavailable
Elevation of Privilege: Gaining higher access than permitted
Now that we've covered network-level attacks, let's talk about some specific attack types that pop up regularly in Ethical Hacking Technical Interview Questions, especially for mid to senior roles.
1. What is cryptojacking?
Cryptojacking is when an attacker secretly uses someone else's device to mine cryptocurrency. The victim has no idea their CPU is being drained. It usually gets in through malicious browser scripts or infected software. Detection signs include unusually high CPU usage, slow device performance, and overheating. Security teams look for suspicious outbound connections and abnormal resource consumption to catch it.
2. What is a botnet?
A botnet is a network of infected devices called "bots" or "zombies" all controlled by one attacker through a command-and-control (C2) server. The device owner usually has no idea their machine is part of it. Botnets are used for large-scale DDoS attacks, sending spam, credential stuffing, and spreading malware further. The infamous Mirai botnet, for example, took down major websites by recruiting millions of IoT devices.
3. What is the difference between a brute force attack and a dictionary attack?
Both are password-cracking methods, but they work differently. A brute force attack tries every possible combination: letters, numbers, symbols, until it finds the right one. It will eventually crack any password, but it's slow, especially against long passwords.
A dictionary attack uses a pre-built list of common passwords, phrases, and known leaked credentials. It's much faster than brute force, but only works if the target password is on that list.
In real assessments, tools like Hydra and Hashcat are used for both approaches.
4. What is CSRF (Cross-Site Request Forgery)?
CSRF tricks an authenticated user into unknowingly submitting a request on a web application. For example, you're logged into your bank, and you click a malicious link. That link silently sends a fund transfer request using your active session. The server sees it as a legitimate request because your credentials are attached.
Standard prevention methods:
Anti-CSRF tokens: Unique tokens added to forms that the server verifies
SameSite cookie attribute: Restricts cookies from being sent with cross-site requests
Checking the Referer header: Verifying where requests are actually coming from
5. What is PGP (Pretty Good Privacy)?
PGP is an encryption program used to secure emails, files, and communications. It uses a combination of symmetric and asymmetric encryption; the message is encrypted with a session key, and that key is then encrypted with the recipient's public key. PGP is widely used by security professionals for secure communication and verifying digital signatures.
Knowing attack theory is one thing. Knowing which tool to pick and why is what separates a strong candidate from a great one. Interviewers asking these questions want to see that you've actually used these tools or at least understand them practically.
1. Why is Python commonly used in ethical hacking?
Python is clean, readable, and has a massive library ecosystem that's useful for security work. With Python, you can write custom scripts to automate reconnaissance, build simple port scanners, parse logs, craft network packets using libraries like Scapy, or interact with APIs. It doesn't require compiling, which makes rapid prototyping fast during a live assessment. Most publicly available exploit scripts and security tools also have Python components.
2. What are ports 20 and 21 used for?
Both are associated with FTP (File Transfer Protocol). Port 21 handles the control connection, commands, and responses. Port 20 handles the actual data transfer in active mode. From a security standpoint, FTP sends data, including credentials in plain text, which makes it a target for sniffing attacks. Most security assessments flag open FTP ports as a risk and recommend SFTP or FTPS as replacements.
3. What is a TCP/IP fingerprint?
Every operating system handles TCP/IP connections slightly differently, things like how it sets TTL values, window sizes, and responses to unusual packets. A TCP/IP fingerprint uses these differences to identify the OS of a remote system. This is what Nmap's OS detection feature does. During recon, knowing the OS helps narrow down which vulnerabilities and exploits are relevant.
4. What tools are used for network sniffing beyond Wireshark?
Wireshark is the most popular, but there are others worth knowing:
Tcpdump: Command-line packet analyzer, great for remote servers
Dsniff: A collection of tools designed specifically for sniffing passwords and sensitive data over a network
Ettercap: Used for MitM attacks and live sniffing on switched networks
NetworkMiner: Focused on passive capture and host analysis
These questions look simple on the surface. But they're asked specifically to see if you actually understand the difference or if you're just repeating definitions. Candidates who fumble here often do so because they've memorized terms without understanding the context.
1. What is a backdoor, and how is it different from a Trojan?
A Trojan is malicious software disguised as something legitimate: a useful app, a game, a document. It tricks the user into installing it. Once inside, it can do various things: steal data, create a backdoor, and download more malware.
A backdoor is specifically a hidden method of bypassing normal authentication to access a system. It can be installed by a Trojan, but backdoors can also be planted by insiders, or even accidentally left behind by developers during testing.
Think of it this way: a Trojan is the delivery vehicle. A backdoor is what gets left behind.
2. What is the practical difference between VA and PT — and when is each used?
This question comes up more than you'd think, even in Ethical Hacking Interview Questions for Freshers rounds.
Vulnerability Assessment (VA): Automated scanning to identify known vulnerabilities. Faster, cheaper, gives you a list of issues. Doesn't tell you how far an attacker could actually go.
Penetration Testing (PT): Manual + automated testing where you actually attempt to exploit vulnerabilities. Slower, more expensive, but it shows real-world risk.
Use VA for regular hygiene checks. Use PT when you need to understand the actual impact of a breach, before an attacker does.
3. What is a Script Kiddie?
A Script Kiddie is someone who uses pre-built hacking tools and scripts without actually understanding how they work. They're not writing exploits, they're just running them. The term matters in professional security because it represents the risk from low-skill attackers using widely available tools. Many real-world breaches happen not from sophisticated attacks but from automated tools run by people who barely understand what they're doing.
4. What are DDoS Trojans?
DDoS Trojans are a specific category of malware designed to turn infected machines into bots that launch DDoS attacks on command. Unlike standard DDoS tools, which are run deliberately by an attacker, DDoS Trojans spread themselves and quietly recruit devices, often without the device owner ever knowing. This is how large botnets are built.
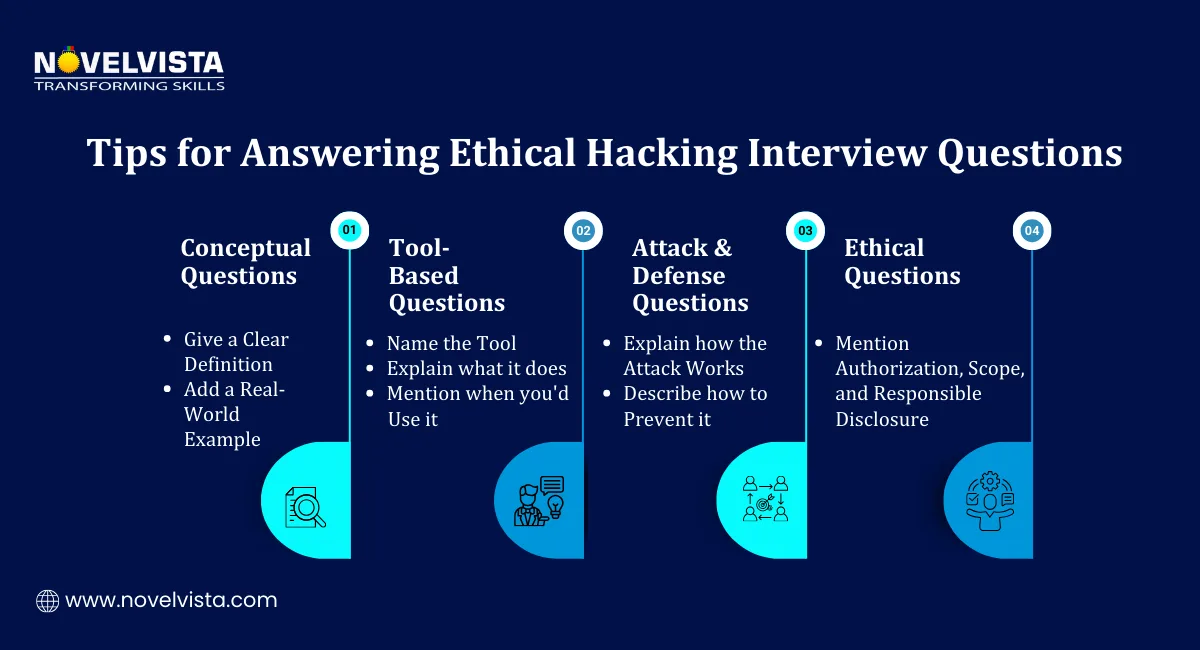
Knowing the answers is half the job. Delivering them clearly under pressure is the other half. Here's what actually works.
For conceptual questions
Don't just drop a definition. Lead with a clear one-line explanation, then immediately follow it with a real-world example. Interviewers remember candidates who make abstract things feel concrete.
For tool-based questions
Name the tool, say what it does in one sentence, then describe a specific situation where you'd use it. "I'd use Nmap during the scanning phase to identify open ports and running services on the target network" is far better than "Nmap is a port scanner."
For attack and defense questions
Always cover both sides. How does the attack work? And how do you stop it? This is especially important in interview questions on ethical hacking for mid to senior roles. Interviewers aren't just hiring someone who can break things; they want someone who understands the full picture.
For ethical considerations questions
Show that you understand the legal and professional boundaries. Mention written authorization, scope agreements, responsible disclosure, and staying within defined test parameters. This tells the interviewer you're a professional, not just a technically skilled person.
One tip that ties everything together
Before any interview, revisit the five stages of hacking. Reconnaissance, scanning, gaining access, maintaining access, covering tracks. A large number of Ethical Hacking Interview Questions for Freshers and experienced candidates alike connect back to this framework in some way. If you can anchor your answers to these stages, your responses will sound structured and confident.
That covers everything, from the foundational concepts freshers need to nail, right through to the advanced exploitation and tool knowledge that senior roles demand. The difference between a good candidate and a great one isn't how many terms they've memorized. It's whether they can explain why something works, how an attacker would use it, and what a defender should do about it.
Go through each section, find the questions you can't answer confidently yet, and practice saying your answers out loud. Not typing them, saying them. That's where the real preparation happens.
Next Step
If you want to go beyond just answering interview questions and actually build the skills that get you hired, NovelVista's Certified Ethical Hacking training course is where to start. You'll get hands-on practice, real-world scenarios, and expert guidance, everything you need to walk into any interview with genuine confidence.
Check out NovelVista's CEH Certification Training and take the first step toward your cybersecurity career.
Author Details
Confused About Certification?
Get Free Consultation Call
Stay ahead of the curve by tapping into the latest emerging trends and transforming your subscription into a powerful resource. Maximize every feature, unlock exclusive benefits, and ensure you're always one step ahead in your journey to success.