Category | Security
Last Updated On 26/03/2026

A lot of people are curious about cybersecurity as a career. Fewer know what the numbers actually look like once you get into it.
The ethical hacker salary in India has grown significantly over the past few years, and 2026 data paints a clear picture of what professionals at different stages can realistically expect to earn.
This guide covers average salary benchmarks, how pay changes with experience, city-wise variations, certifications' impact, top-paying roles, and the skills that push earnings higher.
| Topic | Key Point |
| Average ethical hacker salary | Rs 540,000 per year nationally in 2026 per PayScale |
| Glassdoor benchmark | Rs 500,000 per year |
| Entry-level total compensation | Rs 508,682 |
| Early career in Pune | Rs 1,100,000 |
| Senior-level potential | Up to Rs 4,000,000 per year |
| CEH certified average | Rs 518,850 per year |
| Penetration tester average | Rs 600,000 per year |
| Security engineer average | Rs 1,080,000 per year |
| Top employers | TCS, Infosys, IBM |
| Linux skills salary link | Up to Rs 1,300,000 |
The short answer is yes. The data backs it up clearly.
The ethical hacker salary in India averages Rs 540,000 per year in 2026, according to PayScale. That places it among the more competitive career paths within the broader cybersecurity space. For professionals with experience, certifications, and the right role, the numbers climb significantly higher.
Three things are driving this growth:
The ethical hacking salary in India is growing across experience levels, cities, and role types. Whether you are just starting out or moving into a senior position, knowing where you stand against these benchmarks helps you make smarter career decisions.
In our training batches across 2024–2025, nearly 62% of learners transitioning into cybersecurity reported salary jumps within 6–12 months after moving into hands-on security roles.c
Before looking at how salary varies by experience or location, it helps to establish a clear baseline. Here is what the 2026 data shows across major sources:
| Source | Average Annual Salary |
| PayScale | Rs 540,000 |
| Glassdoor | Rs 500,000 |
The Rs 500,000 to Rs 540,000 range is the most reliable baseline for evaluating ethical hacker salary expectations in India right now. Different sources report slightly different figures because they draw from different samples. But the consistency across them confirms this range as a solid reference point.
A few things worth noting:
For anyone evaluating whether to enter this field or comparing their current salary, this range is the right starting point.
Experience is the single strongest driver of ethical hacker salary growth in India. The jump from entry level to senior is significant, and the numbers reflect genuine market demand for skilled professionals at every stage.
Fresh entrants to the field can expect average total compensation of around Rs 508,682. At this stage, most professionals are building foundational skills across:
Certifications like CEH help at this level. They compensate for limited hands-on experience and signal to employers that the candidate has verified, structured knowledge rather than just self-study.
In entry-level training programs we conduct, candidates with lab-based project experience typically secure offers 15–20% higher than those with only theoretical certification preparation.
This is where the ethical hacking salary in India starts to move meaningfully. Key figures for this stage:
The Pune figure is notably higher than the national average for the same experience band. This reflects the concentration of IT and cybersecurity employers in the city and the premium they place on professionals who combine practical skills with recognized credentials.
The salary of ethical hacker professionals at senior levels can reach up to Rs 4,000,000 per year. That is nearly eight times the entry-level figure. This kind of growth does not happen on time alone. It comes from:
| Experience Stage | Average Annual Salary |
| Entry level (0 to 1 year) | Rs 508,682 |
| Early career national average | Rs 692,087 |
| Early career in Pune | Rs 1,100,000 |
| Senior level | Up to Rs 4,000,000 |
Where you work has a real impact on the professional hacker salary you can expect. Cities with strong tech ecosystems offer faster salary growth, more employer options, and better access to senior roles.
Here is how five major cities compare based on available data from PayScale, Glassdoor, and industry reports.
Pune has established itself as one of the stronger markets for cybersecurity professionals in India. The numbers tell an interesting story:
The gap between these two figures is significant. Early career professionals who land the right roles in Pune benefit from a fast salary ramp that outpaces the national average considerably. The overall average is pulled down by a broader mix of experience levels, but for professionals in the one to four year range, Pune is one of the best-paying markets in the country.
Bangalore is India's primary tech hub and consistently ranks among the highest-paying cities for cybersecurity roles.
Key reasons Bangalore commands a premium:
Mumbai brings a different kind of demand to the cybersecurity market. The city's dominance in BFSI: banking, financial services, and insurance creates a strong and consistent need for ethical hackers who understand regulated environments.
Professionals with knowledge of compliance frameworks like RBI guidelines, PCI-DSS, and ISO 27001, alongside ethical hacking skills, command a notable premium in Mumbai compared to purely technical profiles.
Hyderabad has grown rapidly as a cybersecurity market over the past five years, driven largely by the expansion of global capability centers and IT services firms in the city.
What makes Hyderabad attractive:
Kolkata shows a different pattern compared to major tech hubs:
The flat progression between entry level and early career points to a slower salary growth curve in the early years. This does not make Kolkata a poor market for ethical hackers overall. But it does mean professionals there may need to be more proactive about:
Our placement and corporate upskilling data across Pune, Bangalore, and Hyderabad consistently shows location-based salary differences of up to 25% for identical skill profiles.
| City | Average Annual Salary | Notes |
| Bangalore | Rs 600,000 to Rs 700,000 | Highest overall demand and employer density |
| Mumbai | Rs 550,000 to Rs 650,000 | BFSI sector premium for compliance-aware profiles |
| Hyderabad | Rs 520,000 to Rs 600,000 | Growing GCC presence, lower cost of living |
| Pune | Rs 478,895 overall, Rs 1,100,000 early career | Fast early career ramp in the right organizations |
| Kolkata | Rs 500,000 flat across entry and early career | Slower progression curve, proactive moves needed |
Certifications are one of the most direct ways to increase your ethical hacker salary beyond standard experience progression. They signal verified, specialized skills to employers and open doors to higher-paying roles that are not accessible without them.
Here is how the main certifications stack up in terms of salary impact.
The CEH is the most widely recognized entry point into professional ethical hacking. Key salary figures:
The CEH credential works best as a baseline. It tells employers you have structured, verified knowledge of ethical hacking concepts and methodology. For professionals just entering the field, it provides a measurable salary advantage over uncertified peers at the same experience level.
OSCP is a more advanced, hands-on certification focused specifically on penetration testing. It is widely respected by employers because it requires candidates to demonstrate real exploitation skills in a controlled lab environment, not just pass a multiple-choice exam.
OSCP is typically pursued after one to three years of experience and aligns with mid to senior-level ethical hacker salary bands. It is one of the stronger signals for penetration testing and red team roles.
CISSP Certification sits at the senior end of the certification landscape. It covers security architecture, risk management, and governance alongside technical skills. Professionals holding CISSP typically move into roles like security engineer or cybersecurity consultant, both of which carry salary bands well above the national average.
The biggest salary gains come when certifications and experience are combined rather than treated separately. Here is a simple way to think about it:
Each certification builds on the previous stage of experience rather than substituting for it. The professionals earning the highest cyber security ethical hacking salary in India are typically those who have combined multiple certifications with genuine hands-on experience over several years.
Prepare with 100+ structured questions covering networking, web security, penetration testing,
and real-world scenarios to build strong concepts and confidently handle cybersecurity interviews.
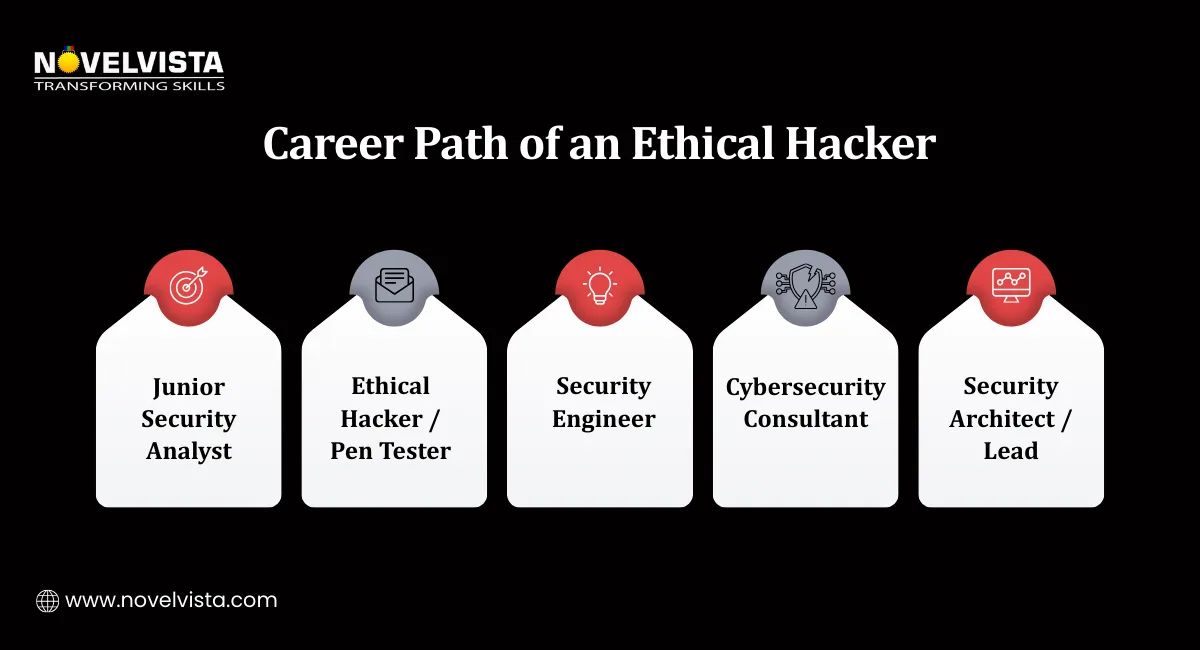
Role title matters as much as experience when it comes to certified ethical hacker salary outcomes. Moving from a generalist security position into a specialist role can accelerate earnings significantly, even without a change in organization.
Here is how the top roles compare on average annual salary:
| Role | Average Annual Salary |
| Penetration Tester | Rs 600,000 |
| Cybersecurity Consultant | Rs 1,000,000 |
| Security Engineer | Rs 1,080,000 |
1. Penetration Tester
Penetration testers are specialists who simulate real attacks on systems to find vulnerabilities before malicious actors do. The role requires strong technical skills across network security, web application testing, and social engineering. It is the most direct application of ethical hacking skills and commands a salary above the national average.
Key skills employers look for:
2. Cybersecurity Consultant
Consultants work across multiple clients and projects, advising organizations on security posture, compliance, and risk management. The role combines technical knowledge with communication and business awareness.
The Rs 1,000,000 average reflects both the seniority required and the value consultants bring across different client environments. Consultants often work for IT services firms or operate independently after building a strong track record.
3. Security Engineer
Security engineers design and implement security systems, processes, and controls at an organizational level. It is one of the highest-paying specialist roles in the ethical hacking space, with an average of Rs 1,080,000 per year.
The role typically requires:
Across enterprise training programs with large IT firms, penetration testing and security engineering roles consistently account for over 55% of advanced cybersecurity hiring demand.
The organizations offering the highest professional hacker salary outcomes are typically large IT services firms and multinational corporations with significant security operations:
These employers operate primarily in major tech hubs, which is another reason city choice matters when optimizing for salary outcomes.
Beyond experience, certifications, and role title, several other factors consistently affect ethical hacking salary in India. Understanding these helps professionals identify where they have the most leverage to increase their earnings.
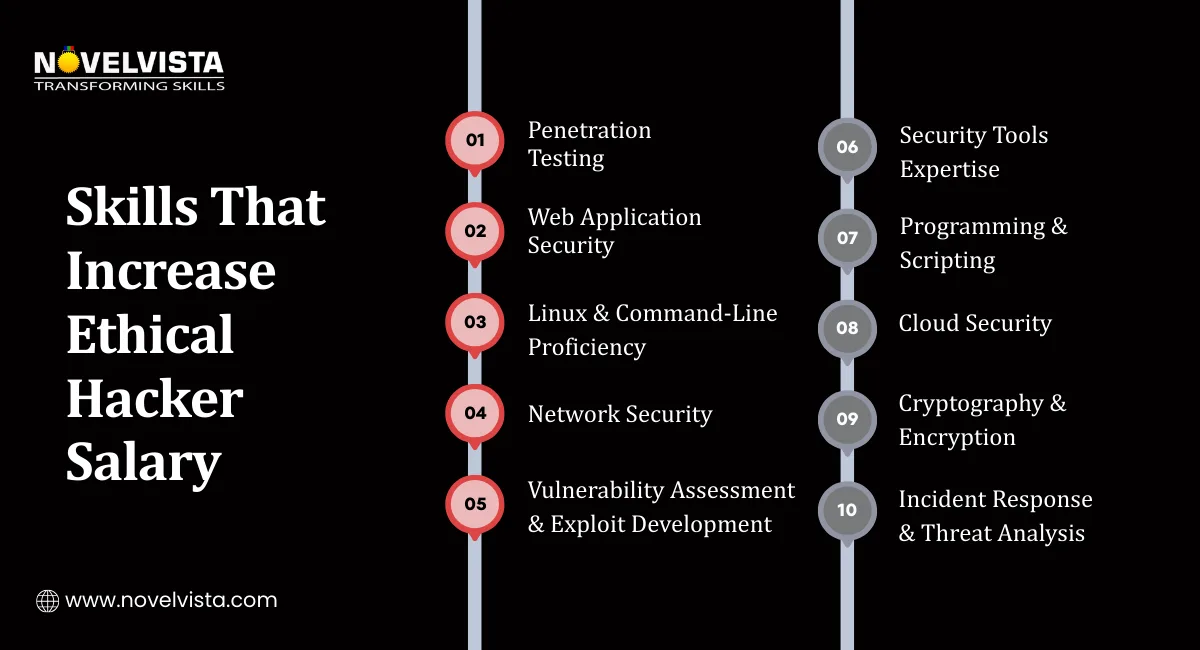
Specific technical skills carry measurable salary premiums. The data is clear on which skills employers value most:
A Bachelor's degree in a relevant field, such as computer science, information technology, or cybersecurity, typically corresponds to an ethical hacker salary range of Rs 540,000 to Rs 720,000.
Education provides the foundational knowledge base, but it is generally less decisive than certifications and hands-on experience in determining actual salary outcomes. Employers in this field consistently prioritize demonstrated skills and credentials over academic qualifications alone.
Several additional factors shape the salary of an ethical hacker in India at the individual level:
The professionals earning the highest ethical hacker salary in India are not necessarily the ones with the most years of experience. They are the ones who have combined the right technical skills, relevant certifications, a specialist role title, and a location or employer that values cybersecurity expertise appropriately.
Each of these factors is individually controllable. Together, they create a meaningful earnings advantage over professionals who have only focused on one or two of them.
NOTE: All salary figures mentioned in this blog are sourced from Payscale and Glassdoor and are intended to reflect general market trends.
The ethical hacker salary in India in 2026 ranges from around Rs 500,000 at the entry level to Rs 4,000,000 or more for experienced senior professionals. That range reflects a career path with genuine growth potential across every stage.
The clearest path to a higher certified ethical hacker salary combines hands-on experience with recognized credentials like CEH or OSCP, a move into specialist roles like penetration testing or security engineering, and strategic choices about location and employer. Technical skills in areas like Linux and web security add further salary leverage on top of that foundation.
From our learner outcomes tracked over two years, professionals who combined certifications, lab practice, and job-switch strategy saw average salary growth of 40–65% within three years.
As India's cybersecurity landscape continues to expand, the salary of ethical hacker professionals are expected to rise further. The demand is structural, the skills gap is real, and the organizations willing to pay competitive salaries for qualified ethical hackers are growing in number across every major industry.
NovelVista's Ethical Hacking Professional Certification Training gives you the hands-on skills and structured knowledge to enter and advance in one of India's fastest-growing cybersecurity career paths. From foundational ethical hacking concepts to advanced penetration testing techniques, the course is built for professionals who want practical expertise that employers recognize and reward.
Explore NovelVista's Ethical Hacking Professional Certification Training and take the first step toward building your cybersecurity career.
Author Details
Confused About Certification?
Get Free Consultation Call
Stay ahead of the curve by tapping into the latest emerging trends and transforming your subscription into a powerful resource. Maximize every feature, unlock exclusive benefits, and ensure you're always one step ahead in your journey to success.