CISA Certification Training and Course | Certified Information Systems Auditor
Advance your cybersecurity career in 2026 with our CISA Certification Course Training. Our CISA course helps IT professionals gain expertise in information systems auditing, control, and security. With exam-focused preparation and expert guidance, you’ll be fully equipped to clear the CISA exam and advance your IT audit and cybersecurity career.
- Industry Expert Trainers
- ISACA Approved Syllabus
- Accredited Trainer
- Online learning session
CISA Certified Information Systems Auditor Course Overview
The Certified Information Systems Auditor (CISA) certification is a globally recognized credential offered by ISACA, designed for professionals who aspire to build expertise in IT auditing, information systems control, governance, and cybersecurity assurance. The CISA Certification validates an individual’s ability to assess vulnerabilities, manage IT risks, ensure regulatory compliance, and strengthen enterprise security frameworks through effective audit practices.
The CISA Course is ideal for IT Auditors, Information Security Professionals, Compliance Officers, Risk Managers, Cybersecurity Consultants, Governance Professionals, System Analysts, and IT Managers seeking to advance their careers in audit and assurance. Completing the Certified Information Systems Auditor CISA Course enhances professional credibility and demonstrates globally recognized expertise in IT governance, risk management, and information systems auditing.
Our Certified Information Systems Auditor CISA Training is designed for professionals who audit, control, monitor, and assess enterprise IT and business systems. The program delivers comprehensive knowledge across critical domains including Information System Auditing, Governance and Management of IT, Information Systems Acquisition and Development, Operations and Business Resilience, and Protection of Information Assets.
NovelVista has trained thousands of professionals and enterprise teams across cybersecurity, governance, cloud, IT service management, and emerging technologies. We offer CISA Certification courses in the USA, India, Canada, the UK, UAE, Saudi Arabia, Australia, Germany, and across the globe in 2026.

What You Will Get?
Learning Outcome: Certified Information Systems Auditor Certification
After the completion of the course, the participants would be able to:
Training Calendar
Lifetime Access
- Self paced videos, assessments, recall quizzes, more
- For more details, reach us at training@novelvista.com
(Includes Only Training)
CISA Course Curriculum
This CISA Course Curriculum covers essential domains, including vulnerability assessment, IT governance, information systems auditing, asset protection, service management, and system acquisition and implementation. Through practical concepts, real-world audit scenarios, and globally recognized frameworks such as COBIT, ITIL, ISO/IEC 27001, and NIST, the CISA training equips professionals with the skills required to assess, secure, and manage modern enterprise IT environments. The curriculum is designed to help learners build job-ready expertise for careers in IT audit, cybersecurity, governance, risk, and compliance.
Module 1: CISA Overview+
Before diving into technical details, this module gives you a solid understanding of what the CISA certification really stands for, and why it matters in today's risk-prone digital ecosystem. Whether you're just starting out or looking to upgrade your IT auditing career, this foundation will set the stage for success.
- Introduction to CISA Certification: Learn about the CISA certification, its global recognition, and the career opportunities it opens up for IT auditors. This module sets the foundation for understanding the importance and impact of this certification.
- CISA Domains:Understand the five key domains: IT Governance, Risk Management, Systems Acquisition, Security, and Audit. These domains encompass the core areas of focus for auditors and help in assessing systems effectively.
- Role and Responsibilities of a CISA: Explore the responsibilities and duties of a Certified Information Systems Auditor certification. This includes planning audits, identifying risks, ensuring compliance, and ensuring security across IT infrastructures..
- Importance of CISA in IT Auditing: Understand the significance of the Certified Information Systems Auditor Certification in the IT audit industry. Learn how it enhances your ability to identify vulnerabilities, ensure regulatory compliance, and implement controls in IT systems.
- Benefits of Obtaining CISA Certification: Discover the career benefits of earning this certification, including enhanced credibility, global recognition, better job prospects, and opportunities for advancement in the field of IT auditing and cybersecurity.
Module 2: Vulnerability Assessment and Identification+
Our CISA training focuses on equipping you with the skills to detect, assess, and report vulnerabilities before they become full-blown threats. Understanding vulnerabilities is key to strengthening any organization’s IT infrastructure.
- Introduction to Vulnerability Assessment: Learn the CISA fundamentals of vulnerability assessment, including the processes and methodologies used to identify weaknesses in IT systems. This module covers the importance of proactive vulnerability management in safeguarding an organization’s assets.
- Types of Vulnerabilities in IT Systems: Understand the various types of vulnerabilities that can exist in information systems, such as software flaws, configuration errors, and network security weaknesses. Knowing these helps auditors identify risk areas effectively.
- Tools and Techniques for Vulnerability Identification: Get hands-on with common tools and techniques used for identifying vulnerabilities, including automated vulnerability scanners and manual penetration testing methods. This section teaches practical skills for real-world application.
- Risk Assessment and Prioritization: Learn how to assess the potential impact and likelihood of identified vulnerabilities. This includes prioritizing vulnerabilities based on their risk to the organization, allowing auditors to address the most critical issues first.
- Reporting Vulnerabilities and Creating Action Plans: Discover how to document and report vulnerabilities clearly, and how to develop action plans for mitigating or eliminating risks. This step is vital for ensuring effective communication with stakeholders and decision-makers.
Module 3: Information Systems Audit and Assurance Guidelines+
Our CISA course provides a deep dive into the principles and practices of auditing information systems. You’ll learn how to evaluate IT environments for security, reliability, and compliance using globally recognized methodologies.
- Overview of Information Systems Auditing: Understand the fundamentals of information systems auditing, including its purpose, methodologies, and the importance of performing regular audits to ensure system security, compliance, and optimal performance.
- Audit Planning and Methodology: Learn the process of planning an audit, including defining the scope, objectives, and identifying the critical systems and processes that require auditing. This foundational knowledge is critical for effective audits.
- Audit Standards and Frameworks: Explore various auditing standards and frameworks, including ISO/IEC 27001 and COBIT, that guide auditors in assessing system effectiveness, security, and compliance. These standards ensure a structured and consistent audit approach.
- Risk-based Auditing Approach: Learn how to prioritize audit activities based on risk assessments, focusing on areas with the highest risk to the organization. This ensures that limited audit resources are focused where they can have the most impact.
- Assurance Services and IT Controls: Gain an understanding of assurance services and how auditors assess IT controls to ensure the reliability and security of information systems. This involves evaluating the effectiveness of security measures, governance, and compliance practices.
Module 4: Auditing Information Systems+
Our CISA Certification equips you with the essential skills to audit modern IT systems effectively. You'll explore how to assess infrastructure, evaluate risks, and report findings with clarity and impact.
- Introduction to Auditing Information Systems: Learn the basics of CISA auditing information systems, including the role of auditors in assessing and evaluating IT infrastructure, software, hardware, and data management to ensure security and compliance.
- Audit Methodologies and Techniques: Explore various CISA Audit methodologies and techniques used in auditing, including sampling, interviews, document reviews, and automated audit tools. These help auditors systematically assess systems and identify areas for improvement.
- Evaluating IT Governance and Controls: Understand how to audit IT governance practices and controls in place. This includes evaluating policies, procedures, risk management practices, and compliance with industry standards to ensure robust IT governance.
- Conducting IT Risk Assessments: Learn how to conduct a thorough risk assessment of IT systems, identifying potential vulnerabilities, threats, and weaknesses that could lead to security breaches or compliance failures. This is a key part of ensuring system integrity.
- Audit Reporting and Communication: Discover the best practices for preparing audit reports and effectively communicating findings to stakeholders. This includes presenting clear, actionable recommendations for mitigating risks and improving systems.
Module 5: Governance and IT Management+
This CISA module dives into the strategic layer of IT, examining how governance, risk, and compliance intersect with business goals. Through Our CISA Certification, you’ll explore essential frameworks, policies, and legal considerations that shape responsible and effective IT management.
- Introduction to IT Governance: Learn the principles of CISA IT governance, focusing on the structures, processes, and policies that ensure IT aligns with business objectives and supports organizational strategy.
- Governance Frameworks and Standards: Explore various governance frameworks and standards such as COBIT, ITIL, and ISO/IEC 38500, which provide best practices for managing IT systems, resources, and compliance in organizations.
- IT Risk Management: Understand how to assess and manage IT risks, focusing on identifying potential threats and vulnerabilities, and implementing controls to mitigate risk, ensuring the stability and security of the IT infrastructure.
- Strategic IT Management: Learn about the role of IT management in shaping and executing an organization's strategy, ensuring that IT investments support overall business goals and deliver measurable value.
- Regulatory Compliance and Legal Considerations: Explore the regulatory landscape affecting IT governance, including laws and industry standards related to data protection, privacy, and IT security. This ensures IT management complies with legal requirements.
Module 6: Information Systems Acquisition, Development, and Implementation+
This CISA module walks you through the complete lifecycle of IT system development, from planning to post-implementation evaluation, ensuring systems are secure, efficient, and aligned with business objectives.
- Overview of the System Development Life Cycle (SDLC): Learn the stages of the System Development Life Cycle (SDLC), including planning, design, development, testing, and deployment. Understand how these stages ensure that systems meet business needs and are delivered on time.
- Acquisition of Information Systems: Explore the process of acquiring information systems, including the selection of vendors, procurement processes, and ensuring that purchased systems align with organizational requirements and security standards.
- Developing Custom Information Systems: Understand the methodologies for developing custom IT systems in-house, focusing on requirements gathering, system design, development, and testing to ensure the final system meets business and technical requirements.
- Implementation of Information Systems: Learn about the CISA implementation phase, including installation, configuration, data migration, and system integration. Ensure systems are tested and deployed effectively to minimize risks and maximize operational performance.
- Evaluating the Effectiveness of Information Systems: Learn how to assess the performance and functionality of new systems after implementation, ensuring they are aligned with business goals, compliant with regulatory standards, and capable of achieving desired outcomes.
Module 7: Information Systems Operations, Maintenance, and Service Management+
Our CISA Training focuses on managing IT systems post-deployment, ensuring they run smoothly, stay secure, and continuously support organizational goals through proven service management practices.
- Overview of IT Operations: Learn the basics of IT operations, which involve managing day-to-day IT activities, including system performance monitoring, troubleshooting, and ensuring that IT services run smoothly to meet business objectives.
- System Maintenance and Support: Explore best CISA practices for the maintenance and support of IT systems, including regular updates, patch management, and troubleshooting to ensure that systems remain secure and operational over time.
- Service Management Frameworks: Understand how frameworks like ITIL and COBIT guide the management and delivery of IT services. Learn how these frameworks help align IT services with business needs and ensure consistent, high-quality service delivery.
- Incident and Problem Management: Learn how to manage incidents and problems effectively, ensuring quick resolution of IT issues and identifying root causes to prevent recurring problems. This is key to minimizing downtime and maintaining business continuity.
- Performance Monitoring and Reporting: Understand how to continuously monitor IT system performance, measure service levels, and generate reports to provide insights into the effectiveness of IT services and highlight areas for improvement.
Module 8: Information Asset Protection+
This CISA module equips learners with the essential skills to identify, secure, and recover valuable digital assets using recognized security frameworks and response strategies.
- Understanding Information Assets: Learn the concept of information assets, which include data, intellectual property, and systems that are critical to an organization’s operations and competitiveness. Understanding these assets is key to their protection.
- Information Security Frameworks and Standards: Explore various information security frameworks like ISO/IEC 27001 and NIST that guide organizations in protecting their information assets through best practices, policies, and risk management strategies.
- Access Control and Authentication: Understand the CISA importance of access control measures, including authentication and authorization processes, to restrict unauthorized access to sensitive information and ensure that only legitimate users can interact with protected assets.
- Data Encryption and Backup: Learn about the use of encryption technologies to protect data both at rest and in transit. Additionally, explore backup strategies to ensure data availability and recovery in case of breaches or disasters.
- Incident Response and Recovery: Understand the process of incident response to quickly detect, respond to, and recover from information security breaches. Learn the importance of having an incident response plan in place to minimize damage and maintain continuity.
Course Details: CISA Course
The CISA training helps professionals develop the skills required to assess IT controls, manage enterprise risks, conduct system audits, and ensure compliance with globally recognized frameworks such as COBIT and ISO 27001. This CISA Certification course prepares learners for successful careers in IT audit and cybersecurity by combining hands-on audit methodologies, risk assessment techniques, and exam-focused preparation with practical business applications. Participants gain globally recognized skills that support career advancement in IT governance, security, compliance, and risk management roles.
What Will I Learn?+
- Understand the IT Auditing Principles Covered in the CISA Course:Learn the core principles and methodologies of IT auditing, focusing on evaluating the effectiveness of IT governance, security, and risk management in organizations.
- Assess IT Risks and Controls:Develop the skills to identify, evaluate, and manage IT risks, ensuring that systems and processes are aligned with industry standards and regulations.
- Perform IT System Audits:Gain hands-on experience in performing system audits, identifying vulnerabilities, and ensuring compliance with best practices and regulatory frameworks like ISO 27001 and COBIT.
- Audit Information Security and Compliance:Understand how to audit the information security and compliance measures within organizations, ensuring data protection, privacy, and operational integrity.
- Create and Communicate Audit Reports:Learn how to document audit findings clearly and effectively, providing actionable recommendations for improving IT systems and governance.
- Prepare for the CISA Exam:Prepare for the CISA Course exam, reviewing key domains and practice materials to ensure success in obtaining the globally recognized certification.
Eligibility+
- IS/IT Auditors:Professionals involved in auditing information systems and ensuring compliance with security and regulatory standards.
- IT Compliance Managers:Individuals responsible for ensuring that IT systems comply with relevant laws, regulations, and internal policies.
- Chief Compliance Officers:Executives overseeing compliance efforts within organizations, ensuring that processes align with legal and regulatory standards.
- Chief Risk and Privacy Officers:Senior leaders responsible for managing risks and safeguarding the privacy and security of organizational data.
- Security Heads:Leaders responsible for establishing and managing IT security strategies and frameworks within an organization.
- Security Managers:Professionals managing day-to-day IT security operations and ensuring the implementation of security controls.
Pre-requisites+
- To be eligible for the CISA Course, candidates must have a minimum of five years of professional work experience in information systems auditing, control, or security.
- This experience ensures that participants have a foundational understanding of IT systems, making the course content more applicable and valuable.
CISA Course Learning Outcome+
Our CISA course offers a range of key learning outcomes designed to equip you with the knowledge and skills required to succeed in the field of information systems auditing. Some of the core learning outcomes include:
- Become a Certified IT Auditor: Successfully pass the CISA Course exam and gain the globally recognized Certified Information Systems Auditor certification credential.
- Enhance Career Opportunities: Open up new career paths and advancement opportunities in IT auditing, cybersecurity, and risk management across various industries.
- Drive IT Security and Compliance: Acquire the expertise to ensure the security, compliance, and integrity of an organization's IT systems, contributing to its overall risk management strategy.
- Lead IT Audit Projects: Gain the skills to take the lead in auditing complex IT systems, managing audit teams, and providing strategic recommendations for system improvements.
- Effectively Manage IT Risks: Develop the capability to assess and mitigate IT risks, ensuring the confidentiality, availability, and integrity of critical business data.
- Apply Real-World Auditing Techniques: Master the ability to apply practical auditing techniques and methodologies, enabling you to handle real-world audit scenarios with confidence.
CISA Training Delivery Style+
Key Benefits+
Our CISA Online training course is built for individuals who wish to expand their skills and job performance and move into the front line position with regard to information systems auditing. If you aspire to be an IT Auditor and attain a higher level in your career, registering with CISA training course is a must for you.
- Global Recognition: The CISA Course Certification is recognized worldwide, validating your expertise in IT auditing, cybersecurity, and risk management, and making you a valuable asset to employers globally.
- Career Advancement: Earning this certification opens doors to senior roles in IT auditing and cybersecurity, providing significant career growth opportunities and increased earning potential.
- Enhance Credibility: This certification adds credibility to your resume, demonstrating your ability to assess, monitor, and secure information systems, ensuring the protection of critical business assets.
- Increased Job Opportunities: Organizations seek CISA-certified professionals for roles in IT auditing, compliance, security, and risk management, leading to more job opportunities across various industries.
- Master Industry-Standard Auditing Practices: Gain expertise in industry-recognized auditing standards and frameworks, such as COBIT and ISO 27001, ensuring your skills are aligned with global best practices.
- Improved Risk Management Skills: Develop advanced skills in identifying, evaluating, and mitigating IT risks, enhancing your ability to protect sensitive information and maintain business continuity.
- Access to a Global Network: As a CISA-certified professional, you gain access to an extensive network of auditors, cybersecurity experts, and professionals in the field, fostering career growth and knowledge-sharing opportunities.
CISA Course Duration+
Key Features+
Our CISA course provided a complete set of key features, important skills and knowledge that will make you a successful professional Information Systems Auditor.
- CISA Training sessions are in an engaging and interactive format.
- Exhibition of concepts with the help of professional examples.
- Self-analysis and group discussions.
- Case studies as the application of the concepts that were taught.
- Vibrant presentations along with individual and team activities.
- Post-training reading suggestions.
CISA® Certified Information Systems Auditor Exam Format

Exam Format - Objective Type, Multiple Choice
Exam Duration - 4 Hour
No. of Questions - 150 (multiple-choice questions)
Total Marks - 800
Passing Criteria - 450+
Certificate - Within 5 business days
Result - Immediately after the exam
Take our FREE 10-questionCISA practice quizto check you're uderstanding
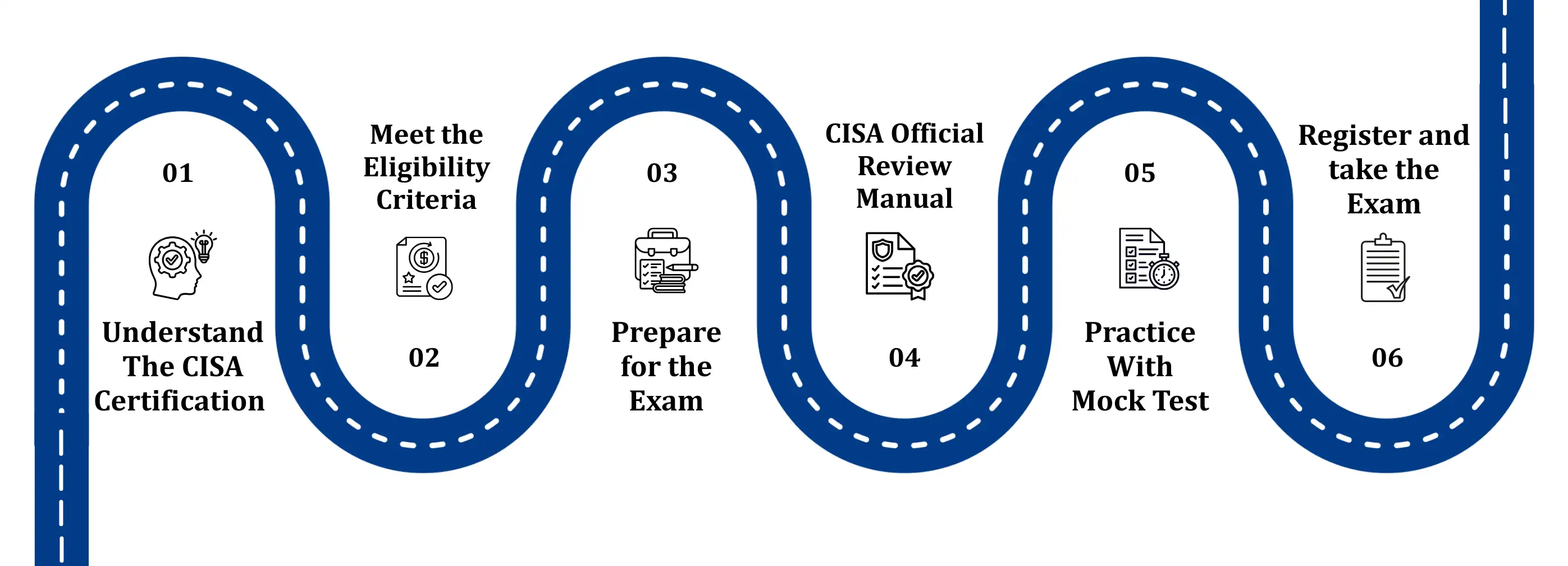
CISA Certification Learning Path