Category | Security
Last Updated On 26/05/2026
In today’s rapidly evolving digital landscape, organizations are increasingly facing complex cybersecurity challenges. As a result, the Certified Information Security Manager (CISM) certification has become one of the most respected credentials for professionals in the information security domain. Whether you’re an experienced security expert or someone eager to enter the field, obtaining CISM certification can significantly boost your career by proving your expertise in security governance, risk management, and incident response.
However, the road to CISM certification can be daunting, especially when preparing for the interview process. Many candidates face challenges, such as skill gaps, lack of preparation, or uncertainty about what to expect. Without proper guidance, it can be difficult to navigate through the tough questions and provide the right answers that highlight your expertise.
In this blog, we will walk you through key CISM interview questions and provide you with well-crafted sample answers, helping you not only prepare for interviews but also gain a deeper understanding of the key areas of information security management. Let’s get started on your journey to securing your CISM certification and taking your career to the next level!
Answer:
What is CISM? (Certified Information Security Manager) is a globally recognized certification by ISACA that validates expertise in managing and governing an enterprise's information security program. It is crucial because it ensures that professionals possess the necessary skills to align security strategies with business objectives, manage risks effectively, and respond to incidents promptly.
Sample Answer:
"CISM is a certification that focuses on the management and governance aspects of information security. It emphasizes aligning security strategies with business goals, managing risks, and responding to incidents. Obtaining this certification demonstrates my commitment to maintaining the confidentiality, integrity, and availability of information within an organization."
Answer:
The four domains of CISM are:
Sample Answer:
"The four domains of CISM provide a comprehensive framework for managing information security. Governance ensures that security strategies align with business objectives. Risk management involves identifying and mitigating risks. Program development focuses on creating and managing security programs, while incident management prepares organizations to respond to and recover from security incidents."
Answer:
Risk assessments are vital as they help identify potential threats and vulnerabilities, assess their impact, and prioritize them based on likelihood. This process ensures that the right resources are allocated to mitigate critical risks.
Sample Answer:
"A thorough risk assessment identifies gaps in security, helps prioritize risks based on business impact, and ensures that resources are allocated to the most critical vulnerabilities, enhancing overall protection."
Answer:
Incident response focuses on managing and mitigating the immediate effects of a security breach, while disaster recovery focuses on restoring the organization’s critical systems and operations following a catastrophic event.
Sample Answer:
"Incident response is about addressing security breaches as they occur, while disaster recovery ensures that an organization can resume essential functions after an event such as a cyberattack or system failure."
Answer:
A security control is any mechanism or procedure used to prevent, detect, or respond to security threats, ensuring the confidentiality, integrity, and availability of data.
Sample Answer:
"Security controls are preventive, detective, or corrective measures that mitigate risks and ensure that organizational data is protected against unauthorized access, alteration, or destruction."
Answer:
A risk register is a document or database that tracks identified risks, their potential impact, mitigation actions, and the risk owner. It is used to monitor and manage risks throughout their lifecycle.
Sample Answer:
"A risk register helps in documenting, assessing, and tracking the organization’s risks. It ensures that mitigation actions are being taken and provides a central point for risk monitoring and management."
Answer:
Defense in depth is a layered security approach where multiple security measures are used to protect information. If one layer is breached, other layers remain intact to provide continued protection.
Sample Answer:
"Defense in depth ensures that security is not reliant on a single control. It combines various techniques, such as firewalls, encryption, and access controls, to protect data at different levels."
Answer:
Encryption is used to protect sensitive data by converting it into a code that can only be deciphered by authorized parties. It ensures that even if data is intercepted, it remains unreadable without the proper decryption key.
Sample Answer:
"Encryption is crucial for maintaining confidentiality, especially for sensitive data transmitted over networks or stored on devices. It ensures that unauthorized access to information is prevented, even if the data is intercepted."
Answer:
I would immediately follow the organization’s incident response plan to contain the breach, assess the damage, notify stakeholders, and work with relevant teams to remediate the issue. Post-incident, I would conduct a root cause analysis to ensure similar incidents don’t occur.
Sample Answer:
"First, I would contain the breach to prevent further damage, then identify and fix the cause. Afterward, I would analyze the incident to strengthen future security measures and report to senior management as needed."
Answer:
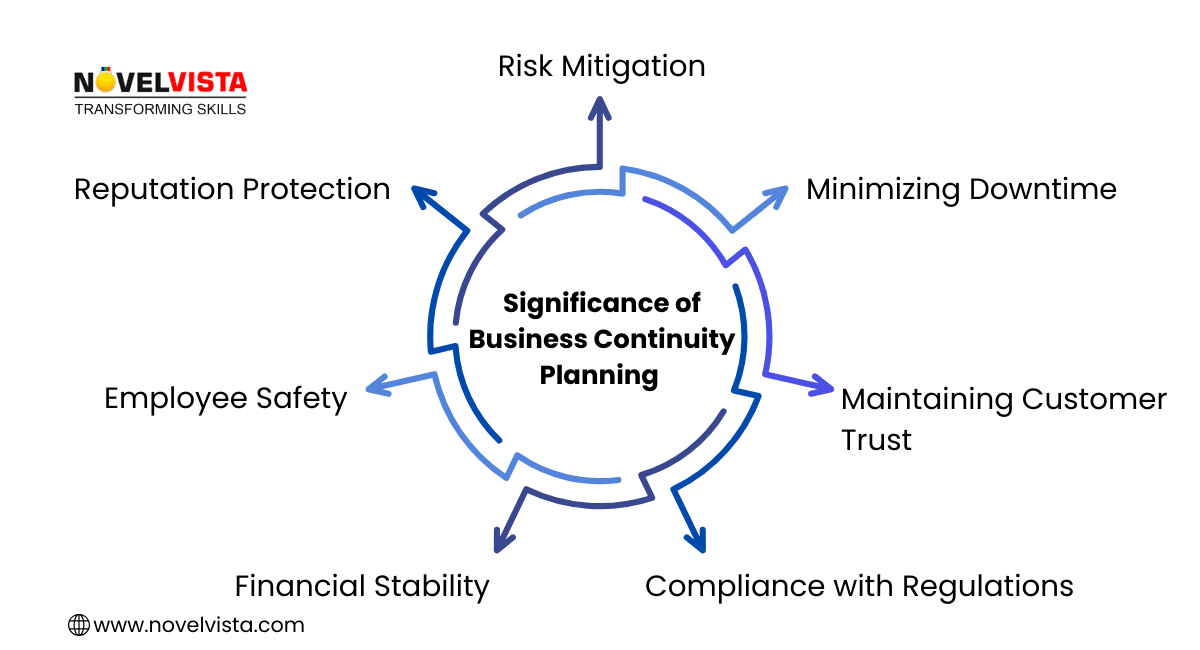
BCP ensures that critical business functions continue with minimal disruption, even in the event of a disaster or security incident. It integrates contingency strategies to keep operations running during and after incidents.
Sample Answer:
"Business continuity planning ensures that essential operations are maintained during disruptive events. It minimizes downtime and enables organizations to quickly recover, protecting both the organization’s assets and reputation."
Answer:
Security controls can be preventive, detective, corrective, or compensatory. Each type plays a distinct role in safeguarding assets by preventing, detecting, correcting, or compensating for security failures.
Sample Answer:
"Preventive controls block threats before they can cause harm, detective controls identify breaches in real time, corrective controls fix issues after they occur, and compensatory controls provide alternative methods for protection when primary controls fail."
Answer:
Compliance ensures that the organization’s security policies, practices, and controls meet the legal, regulatory, and industry requirements. It helps avoid penalties, legal risks, and reputational damage.
Sample Answer:
"Compliance is about aligning security practices with legal and regulatory standards, ensuring that the organization avoids penalties while maintaining a secure and trustworthy environment for its customers and stakeholders."
Answer:
A security framework like NIST or ISO 27001 provides a structured approach to information security, ensuring that all security risks are addressed systematically. These frameworks help organizations create a culture of security and compliance.
Sample Answer:
"Adopting a framework like ISO 27001 helps organizations manage information security risks more effectively by providing established guidelines for securing data and ensuring that processes are aligned with international best practices."
Answer:
A vulnerability assessment identifies weaknesses in an organization’s systems and networks that could be exploited by threats. It is essential for proactive risk management, allowing organizations to patch or mitigate vulnerabilities before they are exploited.
Sample Answer:
"By performing regular vulnerability assessments, organizations can identify and address potential weaknesses in their security posture, reducing the likelihood of successful cyberattacks or breaches."
Answer:
I conduct thorough assessments of third-party vendors, ensuring they follow appropriate security practices. I also implement contractual security clauses and regularly audit their compliance.
Sample Answer:
"Third-party risk management involves evaluating the vendor’s security practices, ensuring they align with our standards, and implementing controls like audits and security clauses in contracts to manage the risks associated with third-party access."
Answer:
Authentication verifies the identity of users or systems to ensure that only authorized individuals or devices can access protected resources. It is crucial in preventing unauthorized access to sensitive data.
Sample Answer:
"Authentication, particularly through multi-factor methods, is essential in protecting against unauthorized access. It ensures that only verified users or devices are granted access, safeguarding sensitive information."
Answer:
I measure effectiveness by using KPIs such as incident response times, breach detection rates, and audit findings. Regular internal audits and compliance assessments also help evaluate the program’s success.
Sample Answer:
"Assessing the effectiveness of a security program involves tracking key metrics such as response time to incidents, breach detection rates, and audit results. This helps ensure continuous improvement in the security posture."
Answer:
The principle of least privilege restricts access rights to the minimum necessary for users to perform their job functions. It minimizes the potential for internal threats and limits the damage caused by compromised accounts.
Sample Answer:
"By granting users the least privilege required for their tasks, the risk of accidental or malicious misuse of data is minimized, thus strengthening the organization’s security framework."
Answer:
Firewalls act as a barrier between trusted internal networks and untrusted external networks. They filter traffic based on predefined security rules, preventing unauthorized access and protecting against external threats.
Sample Answer:
"Firewalls are critical in defending against unauthorized access and potential attacks by inspecting and controlling network traffic. They are the first line of defense against external threats."
Answer:
Data classification involves categorizing information based on its sensitivity. Common categories include public, internal, confidential, and highly confidential. Proper classification ensures that data is protected according to its value and importance.
Sample Answer:
"Classifying data according to its sensitivity ensures that more stringent controls are applied to protect sensitive and confidential information, reducing the risk of data breaches and ensuring regulatory compliance."
Download the complete list of questions and answers in one click – grab your PDF now!
NovelVista offers a comprehensive CISM certification course that addresses all the domains you need to master. With expert instructors, interactive learning methods, and CISM exam simulations, our training will equip you with the skills to excel in your CISM interview and your career.
To succeed in your CISM interview, focus on:
Enroll in NovelVista's CISM certification course today to take the next step in your career.
Securing a role as a Certified Information Security Manager is a significant achievement. By preparing thoroughly and understanding the key concepts and responsibilities, you can confidently approach your interview and demonstrate your expertise. With the support of NovelVista's training programs, you're well on your way to success.
Author Details
Course Related To This blog
CISM® Certified Information Security Manager
Confused About Certification?
Get Free Consultation Call
Stay ahead of the curve by tapping into the latest emerging trends and transforming your subscription into a powerful resource. Maximize every feature, unlock exclusive benefits, and ensure you're always one step ahead in your journey to success.