Category | Security
Last Updated On 09/12/2025

Let’s start with something simple: most people want to get into cybersecurity, but very few know where the cybersecurity career path actually begins or how to grow without feeling lost. If you’ve ever wondered which role comes first, how to pick the right specialization, or which skills actually matter, this guide clears every doubt in a friendly, easy-to-follow way.
This article gives you a full roadmap, starting roles, mid-level growth, leadership paths, top skills, certifications, and everything you need to build real confidence. You’ll know exactly how to move from beginner to advanced without guessing.
And yes, you’ll see how the cybersecurity career path grows from IT support to architect or CISO with the right steps.
Your journey usually begins with roles that help you build your foundation. These are the starting points that teach you how systems behave, where security gaps appear, and how incidents look in real life. Many professionals start here because these roles give the cleanest, simplest view of how an organisation works.
Help Desk / IT Support: You handle basic user issues, system resets, and access-related requests. This builds your understanding of daily IT operations, which is useful when you move deeper into security roles.
Security Analyst (SOC Tier 1): You monitor alerts, check logs, and handle first-level investigations. This is where you learn early threat patterns and how security tools react to unusual activity.
Junior Pen Tester: You assist senior testers with scanning tools, basic exploitation, documentation, and reporting. This grows your attacker mindset while keeping you on the defensive side too.
These roles are exactly what people refer to when they say Entry-level cybersecurity jobs, and also match what fresh learners in our Security+ and beginner SOC batches experience when they land their first jobs. The responsibilities and skills listed here are based on common patterns we observe while guiding new professionals.
Basic networking
System administration
Log monitoring
Vulnerability scanning
These are the skills that act as your “entry ticket” into deeper security work.
CompTIA Network+
These certifications help confirm your knowledge and make your resume stronger while you climb the cybersecurity career path
Once you settle into entry roles, the next step is building real, hands-on experience. This stage shapes your decision-making. You start understanding attacks, incidents, and the small things that keep systems safe.
Take ownership of small incidents.
Ask to join SOC shifts whenever possible.
Volunteer to work on simple investigations.
Participate in change or patch management tasks.
You’re slowly moving from “task performer” to “problem solver,” which is very important for your long-term cybersecurity career path.
Hands-on labs – Platforms like TryHackMe or HackTheBox help you test real-world attacks safely.
Capture-The-Flag (CTF) – You learn skills by solving challenges that sharpen your mind.
GitHub projects – Show your work publicly and build credibility.
Volunteer audits – Offer support to internal teams or small businesses to learn while helping.
Clear communication
Teamwork
Problem-solving
Documentation habits
These are the skills that make people trust you with bigger responsibilities.
This is where your cybersecurity career path starts getting exciting. You pick a direction — engineering, investigations, cloud security, or governance. Specializations help you shape your identity in the industry.
Security Engineer: You design secure systems, improve configurations, manage firewalls, and work with development teams. This role builds strong technical depth.
Incident Responder / DFIR Specialist: You jump in during attacks, investigate digital evidence, and bring systems back safely. You learn how attackers move and how to block them.
Cloud Security Engineer: You protect workloads on AWS, Azure, or GCP. With most companies shifting to cloud, this role stays in high demand.
GRC Specialist: You help companies follow security standards, apply controls, and manage risks. This role is a blend of compliance and governance.
These specialization paths reflect real transitions we see among learners moving from SOC roles to Cloud Security, DFIR, GRC, or Engineering. We regularly help professionals choose these paths based on current hiring trends and what companies expect.
AWS/Azure/GCP Security Certifications
GIAC GCIA / GCIH
Certifications at this level help you stand out and grow into senior positions later.
Once you have 5–10 years of strong experience, your cybersecurity career path opens doors to bigger responsibilities.
Cybersecurity Architect: You design the entire security structure of an organisation, from networks to cloud to identity.
Security Manager: You guide teams, set policies, manage budgets, and make sure projects move in the right direction.
Director / CISO: You handle security strategy, board-level reporting, business risks, and long-term planning.
Build experience in leading small teams.
Learn how to explain technical things to non-technical teams.
Gain a broad understanding of networks, cloud, governance, and threat landscape.
Focus on stakeholder communication and decision-making.
Leadership roles are less about tools and more about direction, planning, and trust-building across the company.
Know the exact skills that will matter in an
AI-driven workplace. Use this guide to upgrade
your career, close skill gaps fast, and stay future-proof.
The world of cybersecurity changes fast, so knowing which skills matter right now helps you grow without confusion.
Cloud security
Threat hunting
SIEM handling
Pentesting
Incident response
Scripting basics
These are the In-demand cybersecurity skills companies actively look for when hiring.
Clear reporting
Calm thinking during incidents
Stakeholder management
Do small targeted projects
Take focused training
Work with mentors
Learn from open-source communities
These skill requirements match the real hiring needs we hear directly from companies that collaborate with us for training. We built this list using recurring skill gaps that recruiters and tech leads highlight when hiring security talent.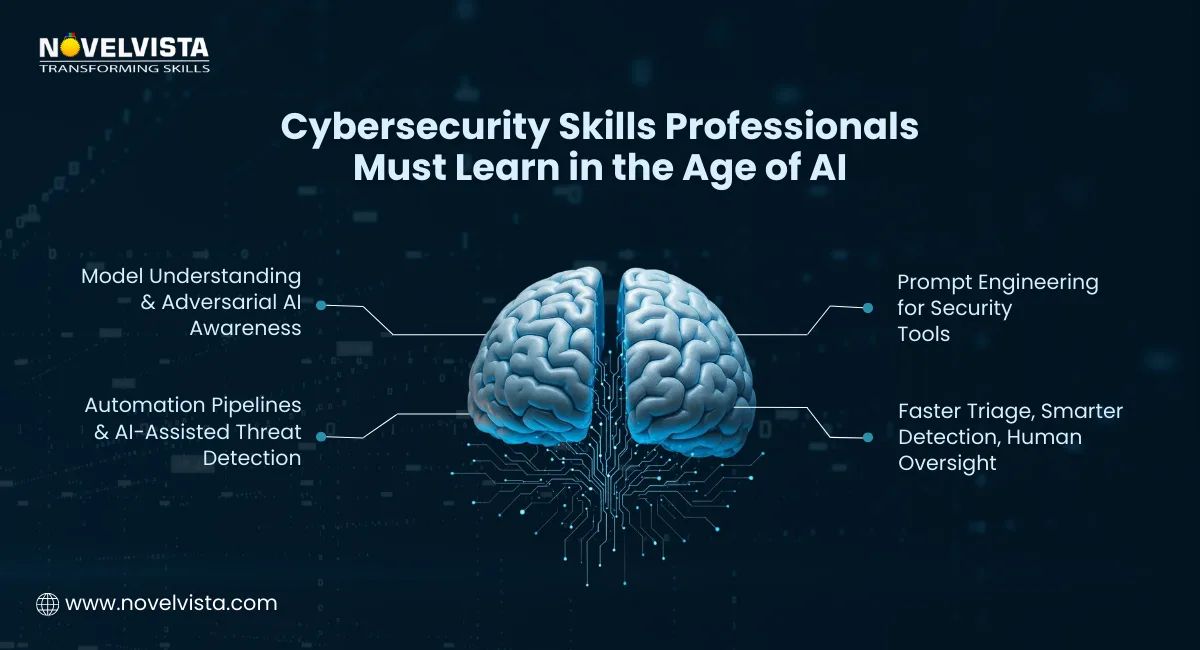
AI is changing how security teams work. Instead of fearing automation, it’s better to learn how to use AI to your advantage.
Understanding basic model behaviour
Using automation for routine tasks
Knowing how attackers may misuse AI
Prompt engineering for security tools
These are known as Cybersecurity skills in the age of AI, and they matter more every year.
Faster incident triage
Better detection accuracy
Easier analysis
More focus on critical decisions that need human judgment
Professionals who mix AI skills with security knowledge move ahead faster in their cybersecurity career path.
For a clearer look at how malware defence is evolving, check out our blog on the future of modern threat protection and emerging security strategies.
Certifications guide your direction, especially when you are unsure which step to take next. They also help build trust with hiring managers because they show that you’re serious about your cybersecurity career path and committed to learning.
CompTIA Security+: Great for building basic knowledge about threats, risks, and everyday defensive tasks. It’s often the first cert many people add to enter Entry-level cybersecurity jobs. (Check out the best pricing)
CompTIA Network+: Helps you understand networks, ports, protocols, and routing basics — skills that matter in almost every security role.
CEH (Certified Ethical Hacker): Helpful for people who enjoy penetration testing and want a deeper attacker mindset. (Check out the best pricing)
OSCP: More advanced, but great for anyone focusing on hands-on exploitation.
Cloud Security Certifications (AWS Solution Architect Associate Certification): These help you secure workloads in the cloud, which matters because the future of cybersecurity jobs shifts heavily toward cloud environments.
CISSP: Best for people moving into senior roles and security leadership.
CISM: Ideal for management roles focused on governance and security program building.
CISA: Great choice for auditing, compliance, and risk-focused careers. (Check out the best pricing)
Choose certifications based on where you want your cybersecurity career path to grow — technical, investigative, cloud-focused, or leadership.
One of the biggest questions people ask is: “How much will I earn as I grow?”
The simple answer — cybersecurity salary improves a lot as you climb each stage, and it keeps getting better with skills and experience.
Entry-level roles ($81K - $140K / ₹3L - ₹7L/yr): You learn the basics, handle daily tasks, and build your foundation. Cybersecurity salary here is decent and rises fast when you gain real incident-handling experience.
Mid-level roles ($107K - $186K / ₹8L - ₹13.0L/yr): Once you specialise (like cloud, DFIR, or pentesting), your value increases because companies look for specific skills. This is where cybersecurity salary jumps the fastest.
Senior and leadership roles ($138K - $239K / ₹9L - ₹64.4L/yr): Architects, managers, and CISOs earn the highest because they impact business decisions and long-term security planning.
Location and cost of living
Industry type (finance and tech pay more)
Hands-on experience
Certifications
Ability to handle incidents calmly
Strong reporting and communication skills
Learn a specialization that companies urgently need
Take on leadership responsibilities
Build a strong portfolio
Consider consulting or freelance projects
The salary insights here come from glassdoor, real discussions with our learners, and career support teams. These patterns reflect what professionals experience while moving from entry roles to specialized and leadership positions.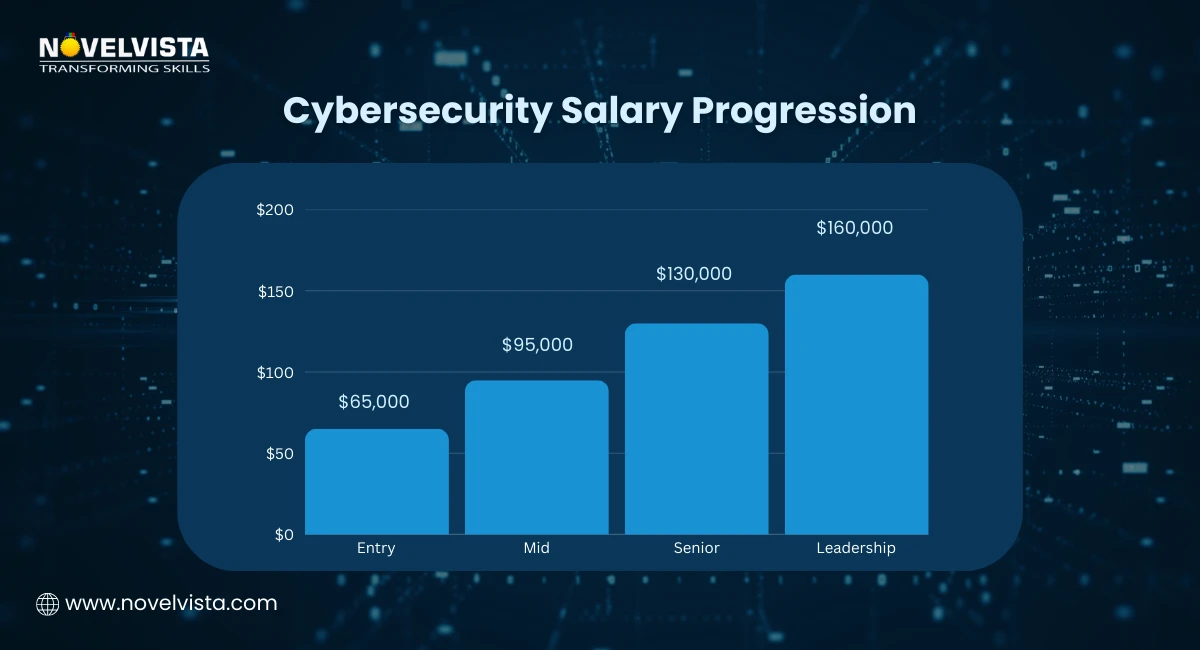
The demand for security talent keeps rising because companies rely on digital systems for almost everything. This means the future of cybersecurity jobs is bright and offers strong opportunities for people who learn steadily.
Cloud Security: Nearly every organization is moving to cloud, opening thousands of new roles each year.
AI-driven defenses: Security tools now use AI for detection and response, so professionals who understand AI gain an advantage.
Privacy and compliance: More regulations mean more auditing and governance roles.
IoT and OT security: Devices like sensors, cameras, and industrial machines need strong protection.
Attacks keep increasing
Companies need 24/7 monitoring
Skills gap is still large
New technologies need new protectors
According to industry reports, 78 percent of organizations say ai is an emerging technology risk. People who stay consistent in their cybersecurity career path will always find opportunities because security remains a global priority.
If you're unsure how to move from beginner to mid-level, here’s a simple, realistic 12-month plan that many professionals follow. It keeps your pace steady without feeling overwhelming.
Build your fundamentals.
Study and pass CompTIA Security+.
Join basic labs or simple SOC projects.
Apply for Entry-level cybersecurity jobs or internships.
Start hands-on labs on TryHackMe, HackTheBox, or cloud platforms.
Join a SOC internship or volunteer for security tasks in your current company.
Start building small GitHub projects.
Choose your specialization: pentesting, cloud security, DFIR, or GRC.
Start studying for a mid-level certification like CEH or cloud security.
Build a portfolio with labs, write-ups, and project notes.
Network with professionals and join community groups.
Apply for mid-level roles that match your chosen path.
This growth plan is inspired by the exact roadmap we give learners who want structured progress. Many of our students follow this sequence and move from beginner to specialized roles within a year.
Both certifications play a huge role for people moving into governance, audit, and management paths.
Best suited for people who want careers in auditing, compliance, and control testing.
It works well for those with 2–3 years of IT or audit experience and want growth in security governance or internal auditing teams. (Check Out the CISA Certification Training)
Perfect for professionals who want to move into management roles. You learn how to build programs, manage risks, and lead teams. A strong choice for people aiming for security manager, consultant, or even future CISO roles. (Check Out the CISM Certification Training)
Both certifications boost credibility and help strengthen your cybersecurity career path in the governance and leadership direction.
Cybersecurity grows through community learning. The more people you meet, the more opportunities you find.
LinkedIn professionals
Security conferences
Local community chapters
Online study groups
Hands-on labs
Webinars
GitHub repositories
Local meetups
Write small blogs
Share learning notes
Publish your projects
Speak at small community events
When people see your work, your cybersecurity career path moves faster because opportunities naturally find you.
Choosing your cybersecurity career path doesn’t have to feel confusing or overwhelming. Once you understand where you stand, what skills you enjoy using, and how the industry is shifting with AI, everything becomes clearer. Every role from analyst to architect, opens a door to learning, growth, and long-term stability.
The key is simple: stay curious, keep upgrading your skills, and follow the area that genuinely interests you. Cybersecurity keeps expanding, and there’s room for people who want to grow with it. You now have a clear map, a direction, and the awareness to make confident moves. Your next chapter in cybersecurity starts whenever you decide to take that first step.
This conclusion reflects the same direction we give to learners who want clarity in their cybersecurity path. Every recommendation here is shaped by real growth patterns we’ve seen in our training programs.
Next Step
If you're aiming for strong credibility in audit or management, NovelVista’s CISA Certification and CISM Certification training programs make the journey easier. You get guided lessons, exam support, real examples, and practical clarity that helps you apply your learning at work. Whether you want to grow in auditing or leadership, these courses help you move forward with confidence. Ready to upgrade your skills?
Author Details
Course Related To This blog
CISM® Certified Information Security Manager
Confused About Certification?
Get Free Consultation Call
Stay ahead of the curve by tapping into the latest emerging trends and transforming your subscription into a powerful resource. Maximize every feature, unlock exclusive benefits, and ensure you're always one step ahead in your journey to success.