Category | Quality Management
Last Updated On 11/11/2025

ISO 27001 risk assessment methodology is the backbone of a strong Information Security Management System (ISMS). Yet, most teams struggle to get it right. Why? Because they either make it overly complex or skip the clarity part, both lead to confusion and poor results.
If you’ve ever felt stuck figuring out where to begin or how to actually write your risk assessment methodology, you’re not alone. This guide is here to help you do it the right way — simple, structured, and practical.
First of all, “What the ISO 27001 Risk Assessment Methodology is?” The ISO 27001 risk assessment methodology is a structured process for identifying, analyzing, and evaluating information security risks to protect an organization's information assets.
In this blog, you’ll learn how to write an ISO 27001 risk assessment methodology step by step, understand what Clause 6.1.2 really means, and get access to an easy, ready-to-use ISO 27001 risk assessment methodology PDF to make your job easier.
Before diving into the steps, it’s important to understand the foundation — Clause 6.1.2 of ISO 27001:2022.
This clause outlines what your organization needs to define and document in its risk assessment approach. It doesn’t tell you exactly how to do it, but it sets the expectations. Think of it as your guiding compass for managing risks in a consistent and repeatable way.
Here’s what Clause 6.1.2 expects you to cover:
In simple terms, Clause 6.1.2 ensures that your risk assessment isn’t random or subjective. It brings structure, accountability, and repeatability to how you identify and treat risks.
 Let’s break it down into simple, actionable steps.
Let’s break it down into simple, actionable steps.
Every good risk assessment starts with clarity. Before you begin listing risks, define why you’re assessing them and where your scope lies.
Here’s how to set the right context:
Establishing context gives you a roadmap. Without it, you might end up wasting time analyzing irrelevant risks or missing critical ones.
Now that you know your scope, it’s time to pinpoint what needs protection.
Start by creating a list of information assets — these could be data, software, hardware, networks, or even people. Then, map out possible threats and vulnerabilities associated with each.
Here’s a simple example:
This step is about visibility. You can’t protect what you can’t see.
Many organizations use structured templates or an ISO 27001 risk assessment methodology PDF to make this part easier. It keeps the documentation clean and consistent.
A few quick tips:
Now that you’ve listed your assets, threats, and vulnerabilities, it’s time to analyze and evaluate them. This is where you decide how serious each risk really is and which ones need urgent attention.
You can approach this in two simple ways:
Once you have both, multiply them to calculate a risk level. For instance:
| Likelihood | Impact | Risk Level | Action Needed |
|---|---|---|---|
| High | High | Critical | Immediate mitigation required |
| Medium | High | Significant | Prioritize control implementation |
| Low | Low | Acceptable | Monitor and review |
This simple table helps you visualize which risks demand quick action and which ones are acceptable within your business limits.
Here’s a tip — don’t overcomplicate the math. A clean, easy-to-read scoring system works better than a fancy one that no one understands.
Once you’ve prioritized your risks, the next step is figuring out what to do about them. This is called risk treatment.
Here’s how it works:
Refer to Annex A of ISO 27001:2022, which lists 93 security controls grouped under four key themes — organizational, people, physical, and technological. Pick the ones that best fit your risk profile.
Create two important records —
The goal isn’t to eliminate all risks (that’s impossible). It’s to reduce them to a manageable level while keeping operations efficient.
When you’re done, you’ll have a clear plan showing how every major risk is being addressed — that’s what auditors love to see.
ISO 27001 doesn’t believe in “set it and forget it.” Risk assessment is an ongoing process, not a one-time task.
Here’s how to keep your methodology alive and effective:
Continuous review is what turns a good ISMS into a great one. It ensures you’re always one step ahead of potential threats.
Identify and manage risks like a pro.
Use this ready-to-edit template to simplify
ISO 27001 compliance and audit preparation.
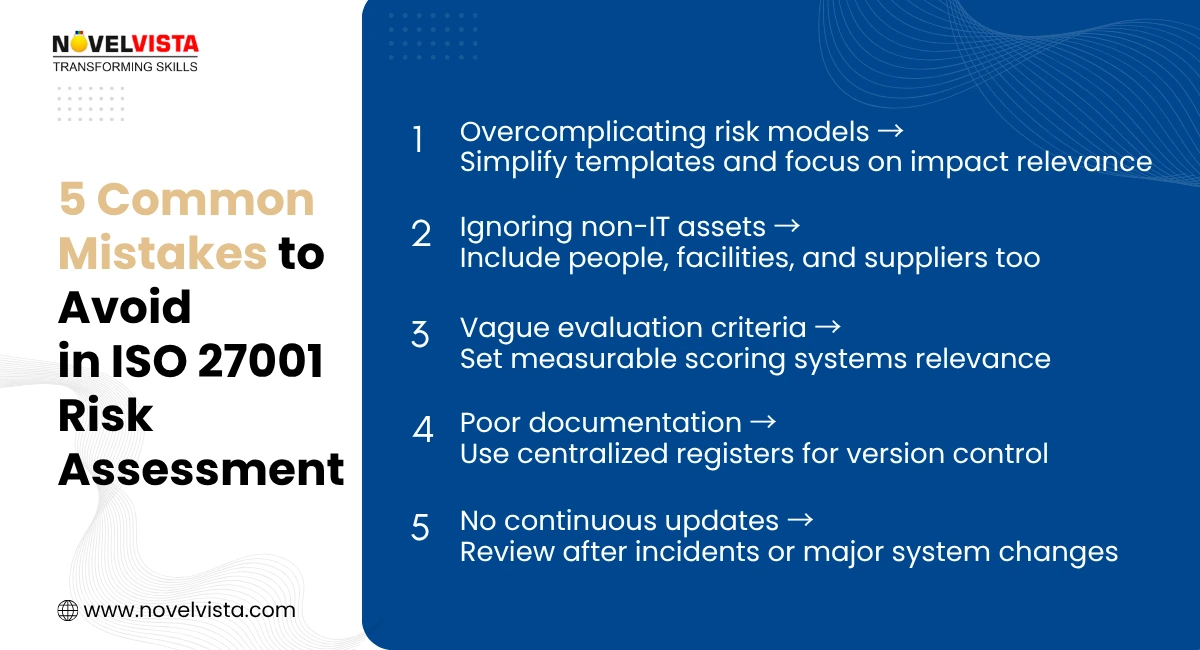
Even with a solid plan, some teams hit common roadblocks when working on their ISO 27001 risk assessment methodology. Here’s what usually goes wrong — and how to fix it:
Solving these challenges often comes down to one word — clarity. Clear process, clear documentation, clear accountability.
Mastering the ISO 27001 risk assessment methodology isn’t just about compliance — it’s about building a culture of proactive security. When your process is consistent, clear, and well-documented, you gain trust, reduce risks, and stay audit-ready at all times.
The best part? Once you document your approach, maintaining it becomes easier each year.
Ready to level up your ISMS skills?
Join NovelVista’s ISO 27001 Lead Auditor Certification Training and learn how to apply risk assessment methodologies in real-world audits. The program helps you master ISO 27001 concepts, gain practical auditing experience, and build the confidence to lead compliance-driven security teams.
Your path to becoming a trusted cybersecurity professional starts here — enroll today and make your next audit your best one yet.
Author Details
Course Related To This blog
ISO 27001:2022 Lead Auditor
Confused About Certification?
Get Free Consultation Call
Stay ahead of the curve by tapping into the latest emerging trends and transforming your subscription into a powerful resource. Maximize every feature, unlock exclusive benefits, and ensure you're always one step ahead in your journey to success.