Category | Quality Management
Last Updated On 11/03/2026

Even mature security teams struggle when discussions turn to ISO 27001 Annex A controls. Some assume Annex A is simply the iso 27001 controls checklist they must follow blindly. Others believe the 2022 update reduced security depth because the number of controls changed. This misunderstanding creates implementation gaps, weak Statements of Applicability, and avoidable audit findings.
In ISO 27001 training and audit preparation sessions, this confusion appears repeatedly. Teams often over-focus on Annex A controls before understanding risk, which leads to misaligned Statements of Applicability and weak audit outcomes.
This guide removes that confusion. It explains what ISO 27001 Annex A controls truly represent, how many controls are in ISO 27001 today, how the new control categories work, and how to implement them correctly using a risk-based approach.
Before discussing Annex A structure, it’s important to answer a common question: what are ISO 27001 controls?
ISO 27001 controls are safeguards or measures designed to reduce information security risks to acceptable levels. They can be technical, physical, organizational, or people-related controls.
In ISO/IEC 27001:2022:
An ISO 27001 controls list typically includes areas such as:
However, ISO 27001 controls are not mandatory by default. They must be selected based on risk assessment results.
During real-world implementations, organizations that treat Annex A as a reference, not a checklist, demonstrate stronger risk alignment and clearer audit justification, especially during Stage 2 certification audits.
ISO 27001 is often misunderstood as a long list of iso 27001 controls to implement. In reality, ISO 27001 is a management system standard. Its core focus is not controls; it’s how security is governed, improved, and aligned with business risk.
ISO 27001 primarily focuses on:
This is why iso 27001 Annex A is not the starting point of an ISMS. The starting point is understanding risk and business context. Annex A Controls exist to support risk treatment decisions, not to replace them.
One of the biggest shifts in ISO/IEC 27001:2022 was how Annex A Controls are organized.
ISO/IEC 27001:2013
ISO/IEC 27001:2022
The new structure groups ISO 27001 Annex A Controls into four clear ISO 27001 control categories:
In transition projects from ISO/IEC 27001:2013 to 2022, organizations that mapped old domains to the 4 new themes early reduced migration timelines by 20–25%. Structured cross-mapping workshops have proven particularly effective in avoiding duplicated technological controls and overlooked organizational responsibilities.
The ISO 27001 Annex A controls are now grouped into four major ISO 27001 control categories. These themes improve clarity, ownership, and accountability across organizations.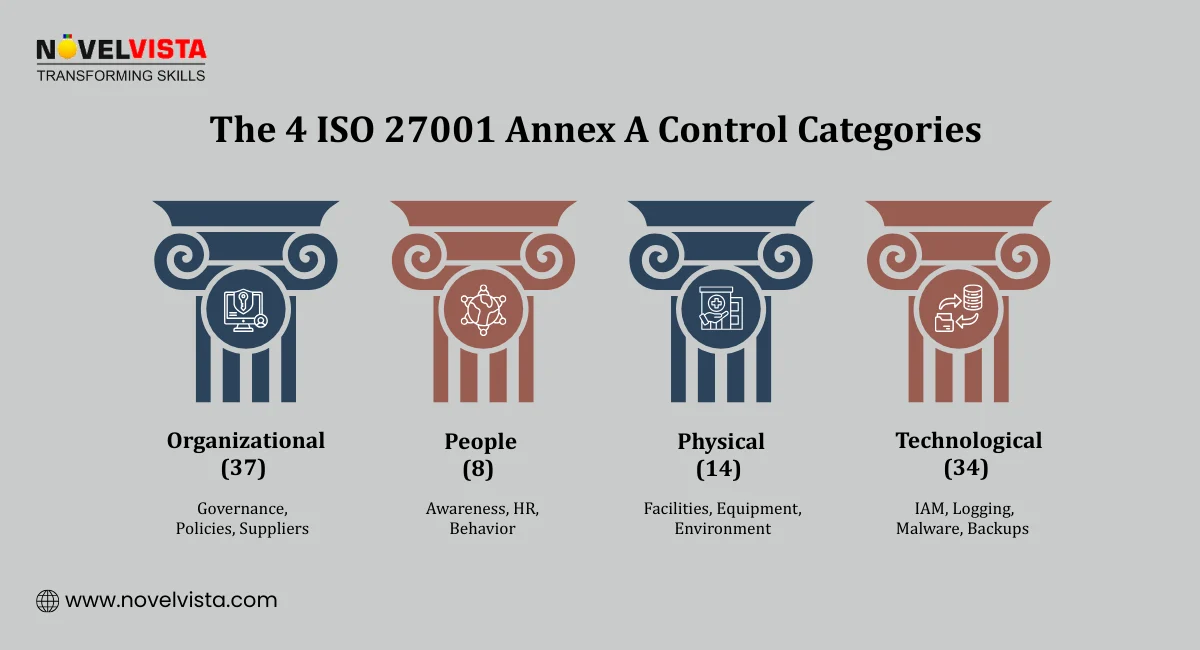
These controls focus on governance, risk management, supplier relationships, asset ownership, and policy frameworks. They ensure management direction and strategic oversight exist. Without organizational controls, security lacks structure and accountability.
Examples include:
These controls form the governance backbone of an ISMS.
People control address human behavior, awareness, training, and employment lifecycle security. Many breaches occur due to human error, making these controls critical.
Examples include:
These controls reduce insider threats and negligence risks.
Physical controls protect facilities, equipment, and physical access points. Even in cloud-first environments, physical protection remains important.
Examples include:
These controls prevent unauthorized physical access or damage.
Technological controls cover system-level protections such as encryption, logging, monitoring, backup, and vulnerability management.
Examples include:
These controls are often supported using tools, automation, and monitoring systems.
The best way to implement ISO 27001 Annex A controls is through a structured, risk-driven process, not through a generic ISO 27001 controls checklist copied from the internet.
Step-by-step approach:
Conduct Risk Assessment First:Identify threats, vulnerabilities, and business impacts before reviewing the iso 27001 controls list.
Select Relevant Controls:From the 93 ISO 27001 Annex A controls, choose those that address identified risks.
Document in the Statement of Applicability (SoA):Clearly justify inclusion or exclusion of each control.
Define Control Owners:Assign responsibility for implementation and monitoring.
Implement with Evidence:Ensure controls are operational and supported by records, logs, or documentation.
Monitor and Improve:Regularly review control effectiveness and update when risks change.
In live ISMS implementations demos, the most stable results are seen when control owners are formally appointed within 30 days of SoA approval. Projects where ownership was unclear experienced delayed evidence collection and audit stress, especially around logging, supplier reviews, and access recertification controls.
Also, using tools such as iso 27001 Annex A controls excel sheets or iso 27001 controls excel trackers can help monitor implementation status, but they should support risk decisions, not replace them.
One of the most misunderstood areas in ISO 27001 implementation is ownership. Many assume ISO 27001 Annex A controls are purely IT’s responsibility. That assumption leads to weak implementation.
In reality, implementing ISO 27001 controls is a shared responsibility across the organization.
Key stakeholders responsible include:
Top Management:Provides leadership, approves risk treatment decisions, and ensures adequate resources are available.
Information Security Manager / ISMS Manager:Coordinates the implementation of the iso 27001 controls list and ensures alignment with risk assessment.
IT Teams:Implement technological controls such as encryption, logging, backup, and access control policy.
HR Department:Handles people controls, including background checks, awareness training, and disciplinary processes.
Facilities / Administration Teams:Manage physical security controls such as secure areas and environmental protections.
Annex A controls are organizational controls, not just IT controls. Accountability must be distributed according to risk ownership.
Many organizations ask:how many controls are there in ISO 27001, and do we need all of them? The answer is93 controlsin ISO/IEC 27001:2022, but not all will apply to every organization.
To identify applicable ISO 27001 controls:
Define Organizational Context:Understand business objectives, regulatory requirements, stakeholders, and scope.
Perform Risk Assessment:Identify assets, threats, vulnerabilities, and impact.
Evaluate Risk Treatment Options:Decide whether to mitigate, transfer, accept, or avoid risk.
Map Risks to Annex A Controls:Select controls that reduce risk to acceptable levels.
Justify Exclusions:If a control is not applicable, document the reason clearly.
In risk assessment workshops, teams that quantify impact using financial or operational downtime metrics produce stronger control justifications. Certification auditors consistently favor measurable risk reasoning over generic statements such as “industry best practice,” particularly when evaluating SoA exclusions.
When implemented correctly, ISO 27001 provides more than certification — it strengthens governance, operational resilience, and customer trust.
Key benefits include:
Structured Risk Management:Clear visibility into security risks and structured treatment decisions.
Improved Audit Readiness:Well-documented iso 27001 controls list and SoA reduce audit stress.
Regulatory Alignment:Supports compliance with data protection and industry regulations.
Stronger Access Management:Clear access control policy ISO 27001 enforcement reduces unauthorized access.
Increased Customer Trust:Certification signals commitment to information security.
Operational Consistency:Standardized control implementation reduces ambiguity.
Organizations that understand what are ISO 27001 controls and apply them correctly gain both compliance assurance and operational discipline.
Annex A was never meant to be the ISMS itself. It is a tool — one that supports risk-driven, business-aligned security decisions.
When teams understand control intent, justify applicability, and continuously improve, Annex A Controls become practical and effective. Security becomes integrated, measurable, and resilient.
The goal is not to “implement all controls,” but to apply the right controls for the right risks — and keep improving as those risks evolve.
If you want to move beyond implementation and develop true audit competence, NovelVista’s ISO 27001 Lead Auditor Certification Training Course is a strong next step. The program focuses on clause interpretation, ISO 27001 Annex A Controls, audit evidence, and real-world scenarios. You’ll gain the skills needed to assess ISMS effectiveness with confidence and support continual improvement at an auditor level.
Author Details
Course Related To This blog
ISO 27001:2022 Lead Auditor
Confused About Certification?
Get Free Consultation Call
Stay ahead of the curve by tapping into the latest emerging trends and transforming your subscription into a powerful resource. Maximize every feature, unlock exclusive benefits, and ensure you're always one step ahead in your journey to success.