Category | Quality Management
Last Updated On 31/01/2026

Cyber risk rarely fails because controls are missing. It fails because risks are managed in isolation. Security teams focus on controls, leadership looks for business impact, and risk teams struggle to connect the two. This is where understanding how FAIR NIST CSF ISO 31000 work together becomes important.
Instead of choosing one framework over another, mature organizations combine them. ISO 31000 provides governance and risk thinking, the NIST cybersecurity framework structures cyber controls, and FAIR translates cyber risk into financial terms. This article explains how these three work together to support structured, measurable, and business-aligned cybersecurity risk management.
Many organizations still manage cyber risk as a technical problem. Security teams track vulnerabilities, compliance teams check frameworks, and leadership receives high-level risk ratings with little context.
This gap is exactly why frameworks like ISO 31000, the NIST cybersecurity framework, and FAIR should be used together. Each addresses a different layer of risk. Understanding how FAIR NIST CSF ISO 31000 work together helps turn cyber risk into something leaders can actually act on.
No single framework can fully address cyber risk on its own. Cyber risk touches governance, operations, and finance at the same time.
That’s why organizations often rely on multiple frameworks:
Used together, they form a layered approach to cybersecurity risk management:
This combination avoids overlap and strengthens clarity instead of adding complexity.
See how ISO 31000, NIST CSF, and FAIR work together in real cyber risk decisions. Understand roles, information flow, and ownership, so cyber risk becomes clear, comparable, and decision-ready.
ISO 31000 is a principles-based framework for managing risk across the organization. It does not focus on controls. It focuses on how risk decisions are made.
This is why ISO 31000 becomes the backbone for decision-making before NIST CSF risk management activities begin.
Explore our article on ISO 31000 to understand risk identification, assessment, and treatment in a clear, practical way.
The NIST cybersecurity framework focuses on what organizations do to manage cyber risk at an operational level. It translates risk thinking into actionable practices.
The NIST cybersecurity framework complements ISO 31000 by focusing specifically on cyber risks and controls, rather than enterprise-wide governance.
FAIR adds the missing financial perspective. While ISO 31000 sets direction and the NIST cybersecurity framework structures controls, FAIR answers one key question: How much does this cyber risk really cost us?
This is critical for leadership decisions. FAIR enables organizations to:
FAIR becomes the bridge that connects governance decisions from ISO 31000 with control insights from NIST CSF risk management.

When combined properly, these three frameworks create a complete and balanced approach to cyber risk. This is where the real value shows, and where many organizations finally understand how FAIR NIST CSF ISO 31000 work together in practice.
ISO 31000 sets the “why,” the NIST cybersecurity framework defines the “how,” and FAIR explains the “how much.” Together, they close the loop between strategy, operations, and business outcomes.
Building an integrated approach does not require starting from scratch. It requires aligning what already exists.
This approach ensures cyber risks are evaluated consistently with other enterprise risks.
In day-to-day operations, the integration becomes even clearer.
This workflow shows clearly how FAIR NIST CSF ISO 31000 work together in real environments. Cybersecurity risk management becomes measurable, repeatable, and aligned with business priorities instead of relying on subjective risk ratings.
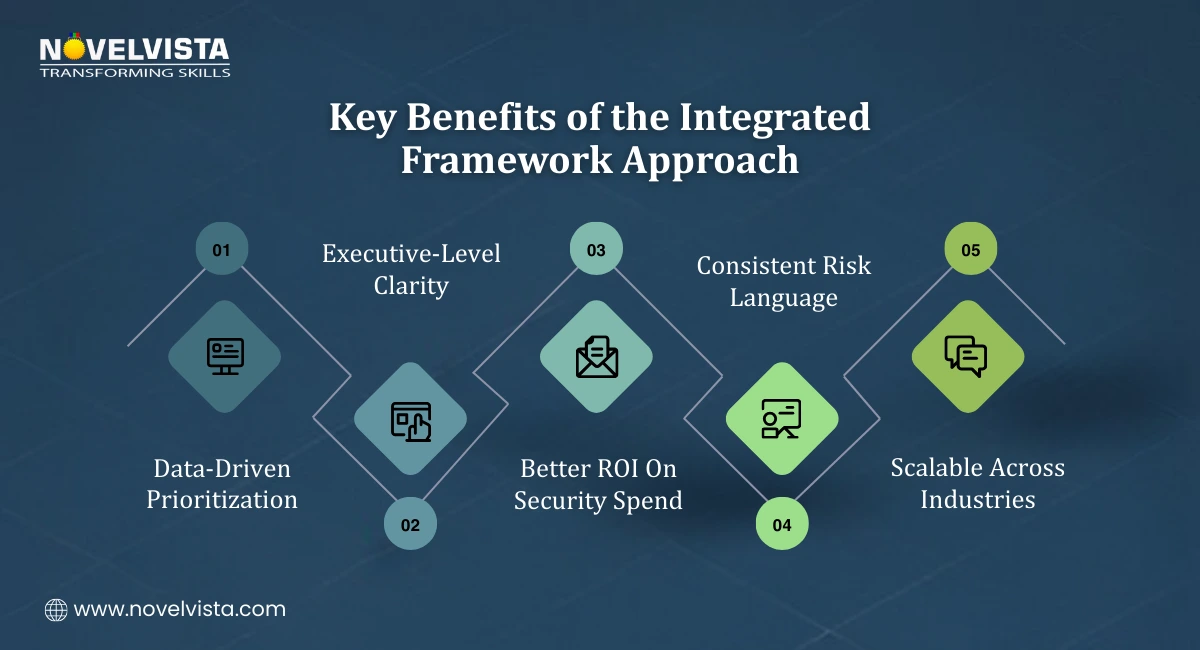
Organizations using this combined model see clear benefits:
By combining governance, controls, and quantification, cybersecurity risk management becomes easier to explain and defend.
To make integration sustainable:
Consistency matters more than complexity. Simple, repeatable practices deliver better results than overly detailed models.
No single framework is enough to manage modern cyber risk. ISO 31000, the NIST cybersecurity framework, and FAIR each solve different parts of the problem.
When used together, they create a mature, measurable, and business-aligned approach to cybersecurity risk management. Understanding how FAIR NIST CSF ISO 31000 work together helps organizations move from Isolated controls to informed, strategic risk decisions that leadership can trust.
If you want to apply this integrated approach with confidence, NovelVista’s ISO 31000 Risk Manager Certification Training is a strong next step. The program focuses on enterprise risk thinking, practical application of ISO 31000 principles, and real-world risk scenarios. You’ll gain the skills needed to align cyber risk with business goals and support informed decision-making at the leadership level.
Author Details
Confused About Certification?
Get Free Consultation Call
Stay ahead of the curve by tapping into the latest emerging trends and transforming your subscription into a powerful resource. Maximize every feature, unlock exclusive benefits, and ensure you're always one step ahead in your journey to success.