Category | Quality Management
Last Updated On 29/01/2026

Cyber incidents don’t just break systems anymore. They disrupt operations, damage trust, and force leadership into tough decisions. That’s why a strong cyber risk management framework can no longer sit only with IT teams.
In our ISO 31000 training programs, we often see organizations struggling not with identifying cyber threats, but with explaining their business impact. Once cyber risks are framed using ISO 31000 language, leadership discussions become clearer and decisions improve noticeably.
This guide explains how to build a practical cyber risk management framework using ISO 31000, apply it to cyber threats, and integrate risk thinking into everyday decision-making.
Cyber threats today are unpredictable, fast-moving, and often linked to business processes rather than just technology. A phishing attack can stop operations. A ransomware incident can halt customer services. A supplier breach can expose sensitive data.
Without a structured cyber risk management framework, organizations react after damage is done. Decisions become rushed, inconsistent, and costly.
ISO 31000 helps avoid that. It offers a way to:
Using iso 31000 cyber security practices shifts the conversation from “how do we fix this?” to “how do we prepare for this?”
The principles of ISO 31000 guide how cyber risks should be managed across the organization.
Cyber risk management should be part of governance, strategy, and operations, not a separate IT activity. A strong cyber risk management framework embeds cyber risk into planning and decision-making.
Cyber risks must be assessed consistently and in a timely way. This avoids ad-hoc decisions and ensures results are reliable.
Every organization faces different threats. ISO 31000 allows iso 31000 cyber security practices to scale based on size, industry, and risk exposure.
Cyber risk visibility improves when IT, business teams, suppliers, and leadership are involved. Inclusive discussions reduce blind spots and improve accountability.
During risk workshops we conduct, inclusive cyber risk discussions often reveal gaps that technical assessments miss, such as supplier dependencies or business process weaknesses. These insights are exactly what ISO 31000 is designed to surface.
For a deeper understanding of risk management fundamentals, explore our blog that takes a deep dive into ISO 31000 principles and shows how they guide effective decision-making.Assess cyber risk as a business risk, not just a technical issue.
Follow a step-by-step ISO 31000 approach to identify, analyze,
and treat cyber risks using real business impact thinking.
Building a cyber risk management framework starts with leadership commitment. Without clear ownership, cyber risk remains unmanaged.
Training and awareness also matter. People need to understand their role in iso 31000 cyber security activities, not just security teams.
Clear communication ensures cyber risk responsibilities are understood across departments, suppliers, and partners.
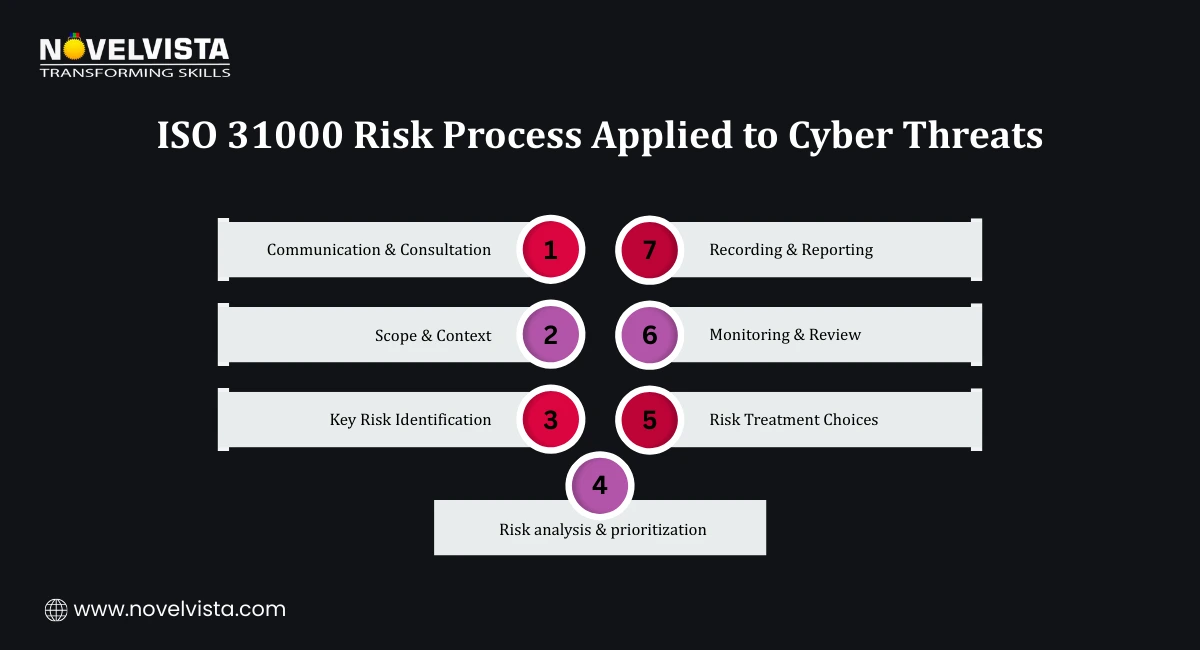
ISO 31000 provides a logical process that fits cyber risk naturally.
This process forms the backbone of an effective cyber risk management framework. In real assessments, organizations that maintain clear cyber risk registers aligned with ISO 31000 are better prepared for audits, incidents, and board reviews. Documentation alone isn’t the strength, the consistency of review and reporting is.
Cyber threats do not stay the same for long. New attack methods, new technologies, and new dependencies keep changing the risk landscape. A practical cyber risk management framework must be flexible enough to evolve.
ISO 31000 supports this by design. It allows organizations to:
Many organizations combine iso 31000 cyber security practices with operational frameworks like NIST CSF. ISO 31000 sets direction and priorities, while operational frameworks support control implementation.
Budget limitations are also common. ISO 31000 helps by encouraging risk-based prioritization. Instead of spreading resources thin, organizations can focus on the cyber risks that matter most to business objectives.

When applied consistently, ISO 31000 delivers clear value beyond compliance.
A well-designed cyber risk management framework also helps build a risk-aware culture. Teams start thinking about cyber risk in daily decisions instead of reacting only during incidents.
This is where iso 31000 cyber security becomes a strategic capability, not just a governance exercise.
Cyber risk management is never a one-time activity. Continuous improvement keeps the framework relevant and effective.
A mature cyber risk management framework evolves alongside the business. As strategy, technology, and partnerships change, cyber risk management must change with them.
ISO 31000 offers a practical and scalable way to manage cyber risks at an enterprise level. When used correctly, it helps organizations move from reactive security measures to informed, structured decisions.
This guidance reflects practical risk management practices used across industries, aligned with ISO 31000 principles and real cyber risk scenarios. The aim is to support informed, consistent decision-making rather than one-time compliance efforts.
A strong cyber risk management framework turns cyber security into a business enabler rather than a cost center. Organizations that apply iso 31000 cyber security practices consistently are better prepared for uncertainty, disruption, and long-term growth.
If you want to apply ISO 31000 confidently in real cyber risk scenarios, NovelVista’s ISO 31000 Risk Manager Certification Training is a practical next step. The program focuses on enterprise risk thinking, real-world case discussions, and hands-on application of ISO 31000 principles. You’ll gain the skills needed to build, adapt, and improve a cyber risk management framework that supports informed leadership decisions.
Author Details
Confused About Certification?
Get Free Consultation Call
Stay ahead of the curve by tapping into the latest emerging trends and transforming your subscription into a powerful resource. Maximize every feature, unlock exclusive benefits, and ensure you're always one step ahead in your journey to success.