Category | DevOps
Last Updated On 07/04/2026

It’s 3:00 AM. Your production database suddenly crashes. Alerts start firing across dashboards, customer transactions fail, and within minutes, your support channels are flooded. Every second feels critical—and every minute of downtime is costing your business more than you can afford.
In 2026, enterprise-scale outages can cost $50,000 or more per minute, depending on the size and digital dependency of the organization. In today’s always-on economy, users expect flawless performance 24/7. One unexpected failure isn’t just a technical issue it’s an immediate threat to revenue, customer trust, and brand reputation.
So what really happens when systems suddenly fail?
Who takes control when alerts start flooding dashboards?
And how do teams respond swiftly without turning incidents into chaos?
This is where SRE incident response becomes a game-changer.
For DevOps engineers, system administrators, IT leaders, and aspiring reliability professionals, mastering SRE incident response is no longer optional it’s essential. It’s not just about fixing problems; it’s about having a structured, scalable approach to detect, respond, and recover while continuously improving system reliability.
In this guide, we’ll explore how modern teams use SRE incident response to move seamlessly from alert to resolution reducing downtime, improving performance, and building truly resilient systems.
SRE incident response is a structured approach used by Site Reliability Engineering (SRE) teams to detect, manage, and resolve system incidents efficiently.
An “incident” refers to any event that disrupts normal service operations like outages, latency spikes, or system failures.
Unlike traditional IT support, SRE incident response focuses on:
It ensures systems remain reliable while maintaining scalability and performance.
In today’s digital-first landscape, downtime is no longer just an inconvenience it’s a business risk.
Here’s why SRE incident response is essential:
Without a proper SRE incident response strategy, teams often react blindly, leading to longer recovery times and repeated failures.
Before diving into tools or processes, it’s important to understand what’s essential for an SRE incident workflow.
A well-defined workflow ensures:
An effective workflow isn’t just about reacting it’s about being prepared.
Let’s break down the essential components of SRE incident workflow that every team should implement:
1. Detection & Alerting
Monitoring systems detect anomalies and trigger alerts. This is the first step in SRE incident response.
2. Triage & Prioritization
Not all incidents are equal. Teams assess severity and prioritize based on impact.
3. Communication
Clear and timely communication ensures everyone stays aligned internally and externally.
4. Mitigation & Resolution
Teams work to restore service quickly, often using predefined runbooks.
5. Post-Incident Review
After resolution, teams analyze what went wrong and how to prevent recurrence.
These essential components of SRE incident workflow create a repeatable and scalable process.
Let’s walk through a typical SRE incident response lifecycle:
Monitoring systems detect unusual behavior such as latency spikes, error rate increases, or infrastructure failures.
The alert is acknowledged, and an incident is officially declared to initiate the SRE incident response process.
The Incident Commander (IC) takes charge, coordinating the response while the Operations Lead (OL) begins technical investigation to identify impacted systems and potential root causes.
If the issue is complex, the IC engages additional experts. The Operations Lead (OL) drives mitigation efforts, while the Communications Lead (CL) ensures stakeholders receive timely and accurate updates.
The OL implements temporary fixes (workarounds, rollbacks, traffic rerouting) to restore service availability as quickly as possible.
The underlying root cause is identified and permanently fixed, bringing systems back to a stable state.
Teams validate that the fix is effective by monitoring system health, confirming service restoration, and ensuring no residual issues remain.
All actions, timelines, decisions, and fixes are documented to create a reliable incident record.
A blameless review is conducted to analyze what happened, identify gaps, and improve future SRE incident response processes.
Learn the step-by-step SRE career roadmap
Master key skills like SLOs & incident response
Explore high-growth opportunities in SRE
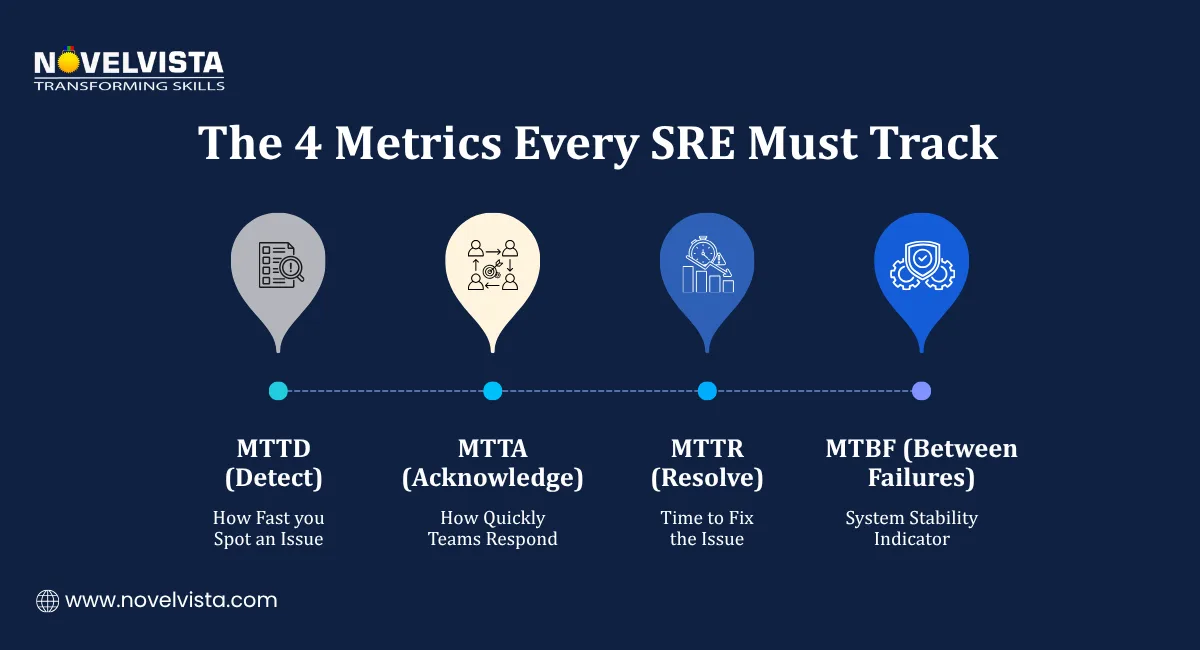
To execute effective SRE incident response, teams rely on a well-integrated stack of observability, alerting, and automation tools that work together to reduce Mean Time to Detect (MTTD) and Mean Time to Resolve (MTTR).
Here are some key categories of tools for rapid incident response SRE teams use, along with widely adopted platforms:
These tools provide deep visibility into system health using metrics, logs, and traces.
These tools help detect anomalies, latency spikes, and resource bottlenecks in real time.
These systems ensure alerts are actionable, routed correctly, and tracked throughout the incident lifecycle.
They centralize alerts, reduce noise, and ensure the right engineer responds at the right time.
Fast, structured communication is critical during high-severity incidents.
These tools ensure seamless coordination between SREs, developers, and stakeholders.
Automation reduces manual intervention and speeds up recovery during incidents.
These tools enable auto-remediation, faster rollback, and consistent execution of recovery steps.
Critical for deep debugging and identifying the exact cause of incidents.
They help correlate logs across systems to pinpoint failures faster.
This emerging category is transforming SRE incident response by enabling faster, smarter decision-making often before a human even gets involved.
These tools use machine learning to:
Impact:
AI-driven triage significantly reduces MTTD and MTTR, allowing SRE teams to focus on resolution rather than investigation.
Pro Tip: Boost your confidence with structured SRE Test Preparation designed to help you master key concepts, practice real scenarios, and excel in your certification journey.
A common question is: how can SRE teams manage incidents effectively?
Here are proven strategies:
Predefined instructions help teams act quickly without guesswork.
Automation reduces human error and speeds up response.
Focus on incidents that affect users the most.
Simulations prepare teams for real-world scenarios.
Transparency prevents confusion during incidents.
Encourage learning instead of assigning blame.
By following these practices, SRE incident response becomes faster, smarter, and more reliable.
Even with the best systems, teams face challenges in SRE incident response:
Too many alerts can overwhelm engineers, causing critical issues to be missed.
Without proper records, teams repeat the same mistakes.
Miscommunication can delay resolution and increase impact.
Using too many tools can create confusion instead of clarity.
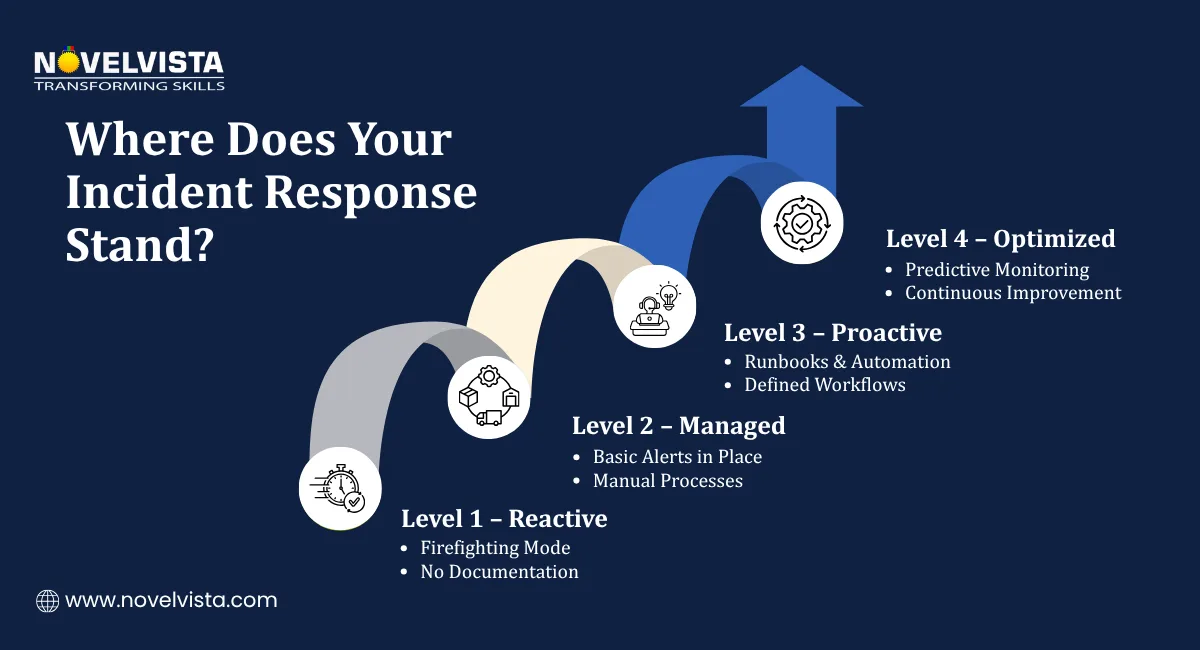
Addressing these challenges is key to improving SRE incident response maturity.
In a world where uptime defines user trust and business success, SRE incident response is no longer a reactive function; it’s a strategic capability. Every alert handled efficiently, every incident resolved quickly, and every lesson learned contributes to building systems that are not just functional, but truly resilient.
A well-structured approach grounded in what’s essential for an SRE incident workflow and reinforced by the essential components of SRE incident workflow enables teams to respond with clarity instead of chaos. When combined with the right tools for rapid incident response SRE teams depend on, organizations can significantly reduce downtime, improve service reliability, and deliver seamless user experiences.
But beyond tools and processes, the real transformation lies in mindset. Understanding how can SRE teams manage incidents effectively shifts teams from constant firefighting to proactive reliability engineering where prevention, automation, and continuous improvement take center stage.
As digital systems continue to scale in complexity, mastering SRE incident response won’t just be an advantage it will be a necessity for IT professionals aiming to lead in the reliability-driven future.
Ready to strengthen your reliability engineering skills and master real-world incident management?
Join NovelVista’s SRE Foundation Training & Certification and gain hands-on expertise in SRE incident response, modern reliability practices, and production-ready workflows. Designed for DevOps engineers, IT professionals, and aspiring SREs, this course equips you with practical knowledge to implement what’s essential for an SRE incident workflow, apply the essential components of SRE incident workflow, and confidently use the right tools for rapid incident response SRE teams rely on.
Start your journey to becoming a high-impact Site Reliability Engineer today!

Author Details
Confused About Certification?
Get Free Consultation Call
Stay ahead of the curve by tapping into the latest emerging trends and transforming your subscription into a powerful resource. Maximize every feature, unlock exclusive benefits, and ensure you're always one step ahead in your journey to success.