Category | Quality Management
Last Updated On 15/01/2026

In an era of always-on systems, cloud platforms, and real-time transactions, audits have evolved far beyond checklist compliance. Today, audits are judged on trust, traceability, and transparency, and regulators expect organizations to prove not just what happened, but exactly how and when it happened. Industry research consistently shows that more than 70% of audit observations stem from weak documentation, missing logs, or broken evidence trails. When records are scattered across systems, lack consistent timestamps, or can be altered without detection, even mature and well-governed organizations find themselves unable to defend their controls.
This is where audit trail techniques move from a supporting control to a critical foundation. They provide auditors with a verifiable, tamper-resistant path to trace actions, transactions, and decisions across systems, departments, and time periods, turning raw data into defensible audit evidence and transforming audits from opinion-based reviews into fact-driven conclusions.
At their core, audit trail techniques provide a structured and verifiable way for auditors to answer four critical questions: who did what, when it happened, and how it was performed. Whether tracing a financial transaction, reviewing system access, or investigating potential fraud, auditors rely on these techniques to follow evidence across systems, departments, and time periods.
As organizations adopt cloud platforms, automated workflows, and integrated ERP systems, the ability to trace evidence end-to-end has become a defining factor in audit quality.
Audit trail techniques are the mechanisms and controls that record, protect, and validate transactional and system activity throughout an organization. They create a chronological record that allows auditors to reconstruct events accurately and reliably.
These techniques play a critical role in:
Regulatory audits (ISO standards, SOX, GDPR, HIPAA)
Fraud detection and prevention
Forensic investigations and incident response
In modern digital ecosystems, where transactions move across applications, APIs, and third-party platforms, manual records are no longer sufficient. Strong audit trail techniques ensure data integrity, support non-repudiation, and protect organizations from compliance failures and reputational damage.
Simply put, without reliable audit trails, audit conclusions lose credibility. Following the ISO 9001 Lead Auditor Checklist helps auditors apply audit trail techniques effectively.
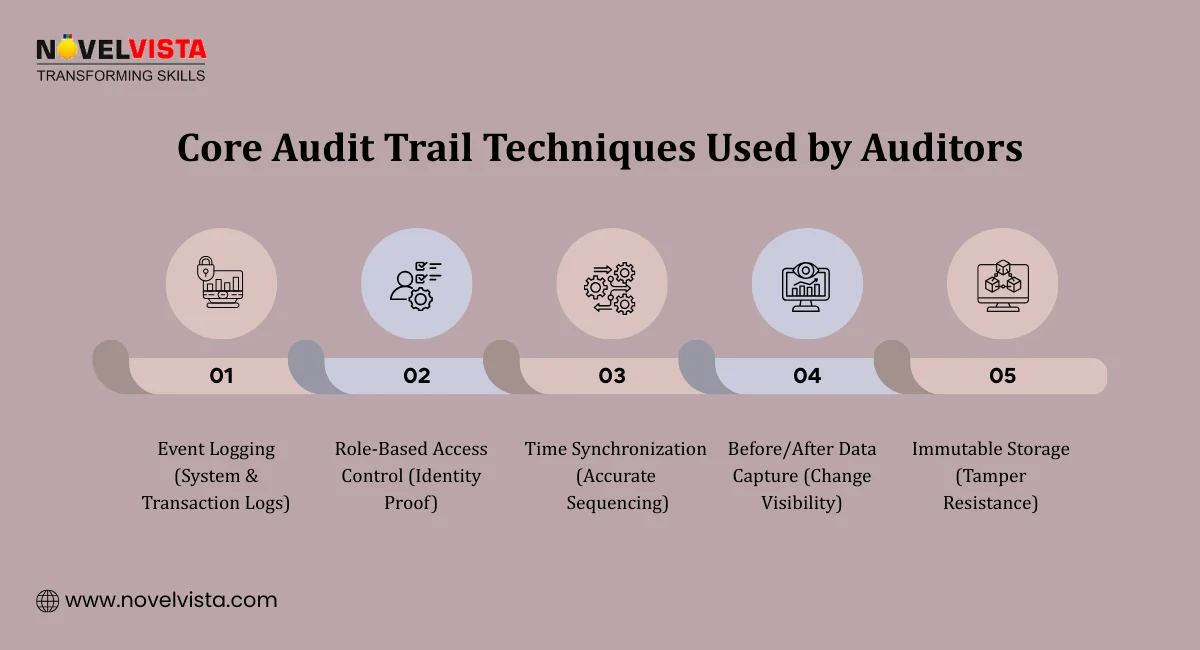 Auditors rely on a combination of technical and procedural methods to ensure traceability. The most effective audit trail techniques include:
Auditors rely on a combination of technical and procedural methods to ensure traceability. The most effective audit trail techniques include:
Automated Event Logging ensures that systems automatically record key activities such as user logins and logouts, data creation, modification, and deletion, as well as financial and operational transactions. By capturing these events in real time without manual intervention, automated event logging minimizes human error, improves accuracy, and ensures a complete and reliable audit trail that auditors can confidently rely on.
Role-Based Access Control (RBAC) links system actions to verified user identities, clearly establishing who performed a specific activity. By restricting access based on defined roles and responsibilities, RBAC strengthens accountability, enforces segregation of duties, and prevents unauthorized actions within the audit trail.
Time accuracy is maintained using NTP synchronization, ensuring events are recorded in the correct sequence, critical for reconstructing timelines.
Detailed Event Logging captures high-quality information such as before-and-after data states, transaction IDs, and digital signatures. These comprehensive logs provide auditors with a clear view of what happened and how it occurred, ensuring transparency and accuracy in the audit trail.
Immutable Storage technologies, such as WORM media and blockchain-based logs, prevent any alteration of records, ensuring that evidence remains tamper-proof. Combined with other audit trail techniques, immutable storage forms the technical foundation for defensible and trustworthy audits.
Aspect |
Horizontal Audit |
Vertical Audit |
| Definition | Reviews similar activities across a defined period or function | Deep dive into a single process, vendor, or transaction chain over time |
| Example | Analyzing all Q1 financial transactions across departments to identify patterns or anomalies | Examining one vendor’s payment trail over several years to detect irregularities |
| Best For | Identifying widespread control weaknesses; comparing consistency across teams or locations | High-risk areas; investigations and root-cause analysis |
| Purpose | Detect trends and systemic issues | Uncover detailed process issues or irregularities |
| Selection Criteria | Based on risk exposure, materiality, and audit objectives | Based on risk exposure, materiality, and audit objectives |
| Combination | Often used alongside vertical audits for stronger coverage | Often used alongside horizontal audits for comprehensive insight |
To auditors, trace evidence means the ability to follow an action or transaction from initiation to final outcome, regardless of how many systems are involved.
A typical evidence-tracing workflow includes:
Define scope – Identify processes, systems, and risks
Collect logs – Gather data from applications, databases, and infrastructure
Correlate events – Match technical logs with business records
Review anomalies – Investigate deviations and exceptions
Learn how auditors trace evidence end-to-end. Build clear, defensible audit trails that reduce follow-ups, strengthen controls, and boost audit confidence.
A well-defined audit workflow ensures audits are repeatable, defensible, and efficient.
Key stages include:
System mapping – Identify data sources, ownership, and interfaces
Evidence correlation – Align logs with invoices, approvals, and contracts
Validation checks – Confirm authenticity and completeness
Documentation – Record findings clearly for reporting and review
By standardizing the audit workflow, organizations reduce subjectivity and strengthen audit conclusions.
To build reliable audit trail techniques, organizations should:
Event scope
Retention periods (e.g., 7 years for SOX)
Access and review rights
Centralize logging, apply encryption, and enforce consistent time synchronization
Automate monitoring using AI/ML to flag unusual behavior and high-risk patterns early
These steps shift audits from reactive reviews to proactive risk management.
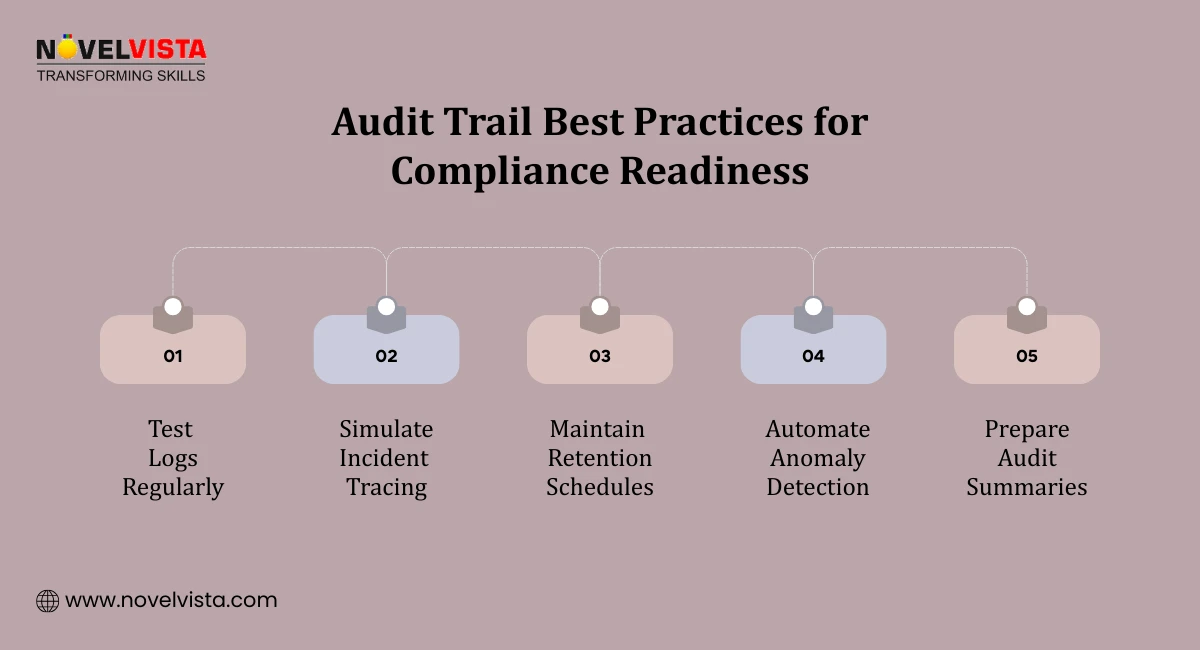 Audit-ready organizations follow key best practices to maintain effective audit trail techniques. They conduct regular testing, including penetration tests and immutability validation, generate clear audit trail summaries for leadership and regulators, and use scalable tools such as Syslog and UEBA-enabled SIEM platforms for continuous monitoring. These practices ensure that audit trails remain reliable, accurate, and effective even as systems and processes evolve.
Audit-ready organizations follow key best practices to maintain effective audit trail techniques. They conduct regular testing, including penetration tests and immutability validation, generate clear audit trail summaries for leadership and regulators, and use scalable tools such as Syslog and UEBA-enabled SIEM platforms for continuous monitoring. These practices ensure that audit trails remain reliable, accurate, and effective even as systems and processes evolve.
Effective audit trail techniques are the foundation of trustworthy, defensible audits. They enable auditors to trace evidence accurately, validate integrity, and draw reliable conclusions in complex digital environments.
By adopting structured audit workflows, correlating technical and business evidence, and balancing horizontal and vertical audit approaches, organizations strengthen both compliance and risk management.
In an era of automation and interconnected systems, robust traceability is no longer a best practice, it’s a necessity for modern, technology-driven audits.
In today’s digital-first world, robust audit trail techniques are essential for trustworthy, technology-driven audits. Structured workflows, evidence correlation, and balanced horizontal vs vertical audit approaches strengthen compliance and reduce risk.
Enhance your auditing expertise with NovelVista’s ISO 9001 Lead Auditor Certification Training. Gain practical skills, real-world insights, and globally recognized credentials to confidently lead audits and implement effective audit trails.
Author Details
Course Related To This blog
ISO 9001:2015 Lead Auditor Training and Certification
Confused About Certification?
Get Free Consultation Call
Stay ahead of the curve by tapping into the latest emerging trends and transforming your subscription into a powerful resource. Maximize every feature, unlock exclusive benefits, and ensure you're always one step ahead in your journey to success.