Category | News
Last Updated On 11/02/2026

The cybersecurity professionals probably felt the year 2025 quite exhausting.
Not because attacks were new — but because they were louder, broader, and far more damaging. The year saw an unusual mix of organized ransomware gangs, nation-state actors, and even teenagers pulling off attacks that caused real economic and social disruption.
What made 2025 different wasn’t just the number of breaches. It was how predictable many of them were.
Weak third-party access controls.
Delayed patching.
Poor asset visibility.
Over-trusted vendors.
Human error at critical points.
The top cyber attacks of 2025 highlighted in this blog weren’t chosen for drama. They were selected based on data loss, recovery cost, service disruption, and geopolitical impact.
Together, they reveal a hard truth:
Many organizations didn’t fail because attackers were brilliant — they failed because governance was weak.
Let’s look at what actually happened.
Two patterns dominated 2025, almost from start to finish.
First, ransomware continued to scale like a business, not a crime of opportunity. Organized groups ran operations with customer support, negotiations, and targeted extortion of executives.
Second, supply chain and third-party attacks exploded. Instead of breaking in directly, attackers abused trusted tools, OAuth connections, service providers, and help desks.
What stood out was the range of attackers:
And the impact went far beyond IT teams.
Airlines grounded flights.
Hospitals lost systems.
Retailers lost hundreds of millions.
Crypto markets were shaken globally.
Cyber risk in 2025 became business risk, plain and simple.

The Clop ransomware group closed out the year with one of the most damaging enterprise attacks.
They exploited CVE-2025-61882, along with weaknesses tied to July patches in Oracle E-Business Suite. Organizations that thought they were “mostly patched” quickly learned otherwise.
Targets included major firms like GlobalLogic and Barts Health NHS. What shocked many was the tactic: direct extortion emails sent to executives, not just IT teams.
Oracle released an emergency patch on October 5, but for many, the damage was already done.
Lesson: Patch timing and asset visibility matter more than patch availability.
The Qilin ransomware group hit Asahi with a classic but devastating data theft attack.
Operations were disrupted until February 2026, and the company’s CEO publicly announced plans to build a dedicated cybersecurity unit after the incident.
Lesson: Incident response planning after a breach is too late.
This attack showed how cyber incidents ripple through entire economies.
The Scattered Lapsus$ Hunters group disrupted Jaguar Land Rover’s systems, affecting over 5,000 organizations connected to its supply chain.
The UK economic impact was estimated at £1.9 billion ($2.55B). Jaguar Land Rover’s revenue dropped 24% in Q3 2025 due to production and sales disruption.
Lesson: Cyber resilience is no longer just an internal issue — it’s ecosystem-wide.
One of the clearest governance failures of the year.
Attackers linked to ShinyHunters and UNC6395 abused Salesloft Drift OAuth access, not Salesforce itself. Once in, they expanded reach using the Gainsight SFDC Connector.
Victims included BeyondTrust, Bugcrowd, Cloudflare, Google, Chanel, Pandora, and many others.
A single trusted integration became a massive breach multiplier.
Lesson: OAuth and third-party access must be treated as high-risk assets.
Two vulnerabilities — CVE-2025-53770 and CVE-2025-53771 — were chained together to compromise 396 on-prem SharePoint systems.
Targets included government bodies and healthcare organizations.
Threat actors ranged from Linen Typhoon and Violet Typhoon to Storm-2603 and Salt Typhoon. These exploits accounted for 40% of Cisco Talos incident response engagements during the period.
Lesson: On-prem systems are not safer just because they’re internal.
The airline sector became a prime target.
The Scattered Spider group breached Qantas systems, exposing data from 5.7 million customers. The entry point wasn’t advanced malware — it was call centers and third-party platforms.
Flights were disrupted, trust was damaged, and recovery took months.
Lesson: People-based access points are as critical as technical ones.
This wasn’t an external breach — it was an insider failure.
Rogue TaskUs agents leaked sensitive data, impacting 70,000 customers. Attackers demanded a ransom, which Coinbase refused to pay. Instead, the company offered a $20 million bounty to identify the attackers.
Estimated losses reached $400 million.
Lesson: Insider risk must be managed as aggressively as external threats.
Retailers across the UK and Europe were hit in rapid succession.
Victims included M&S, Co-op, Harrods, Adidas, Gucci, and others.
UK authorities arrested four teenagers, three of them minors, linked to the attacks.
Lesson: Simple techniques, when repeated at scale, can cripple major brands.
This was the largest crypto theft in history.
North Korea’s Lazarus Group stole $1.447 billion in ETH from Bybit. Q1 2025 crypto losses jumped 303% quarter-over-quarter, reaching $1.67B. By mid-year, losses hit $2.47B, exceeding all of 2024.
Security teams detected 596 phishing domains tied to the campaign.
Lesson: Nation-state attackers treat crypto as strategic funding sources.
Although the incident happened in December 2024, it was disclosed in 2025 — and the impact was serious.
PowerSchool paid a ransom to prevent data leaks involving students and teachers. In May 2025, a 19-year-old attacker pleaded guilty.
Lesson: Youth and simplicity are no longer barriers to serious cybercrime.
When you step back and look at all the top cyber attacks of 2025 together, a few uncomfortable patterns stand out.
First, third-party access and OAuth abuse are no longer edge cases. They are now one of the main ways attackers get in. If a trusted vendor, connector, or service account is compromised, attackers don’t need to break your perimeter — they walk straight through it.
Second, patch delays and asset blind spots continue to hurt even large, well-funded organizations. In several cases, patches existed, but teams didn’t know what systems were exposed or assumed fixes were already in place.
Third, human risk keeps showing up. Call centers, insiders, support teams, and contractors were involved in multiple major breaches. Technology failed — but people and process failures failed first.
And finally, ransomware economics are scaling faster than defenses. Attackers are professional, patient, and well-funded. Many organizations are still reactive, responding only after damage is done.
When you look across all major cyber incidents of 2025, the lesson is clear: most breaches were not technical surprises; they were governance failures.
Access is the new perimeter:Attackers no longer break in, they log in. OAuth abuse, third-party access, insiders, and support channels became the easiest paths into large environments.
Patch availability is not protection:Several organizations had patches available but lacked visibility into what systems were exposed or misconfigured. Asset awareness mattered more than patch release dates.
Human and process risks dominate:Call centers, contractors, and internal teams were involved in multiple breaches. Technology failed, but people and process gaps failed first.
Third-party risk multiplies impact:Supply chain and vendor attacks turned single compromises into ecosystem-wide disruptions, affecting thousands of connected organizations.
Ransomware is now an industry:Attackers operated like businesses, organized, patient, and well-funded, while many defenders remained reactive and fragmented.
Together, these attacks showed that cyber resilience depends less on tools and more on structured control, accountability, and governance.
Preparing for 2026 means shifting from reactive security to risk-driven governance. Organizations must treat cyber risk as business risk, with clear ownership and continuous oversight. Third-party access, OAuth integrations, and service accounts need the same scrutiny as internal users. Incident response plans must be tested, not just documented, and access reviews should be routine, not occasional.
Most importantly, security controls must be audited for effectiveness, not existence. Frameworks like ISO 27001 help organizations identify risks early, validate controls, and drive continual improvement.
For professionals, building skills in security governance and auditing is no longer optional. Those who can assess systems end-to-end will help organizations prevent the next wave of failures, before attackers exploit them.
Cut through the hype around AI hacking. Understand how autonomous attack tools really work, where they’re powerful, and where humans still matter, so stay informed, not alarmed.
It’s tempting to look at these incidents and think, “We just need better tools.”
But the truth is harder.
Most of the 2025 attacks weren’t caused by missing technology. They happened because:
This is exactly where Information Security Management Systems (ISMS) come in.
A strong ISMS forces organizations to:
Without governance, security becomes guesswork.
With governance, security becomes repeatable and measurable.
2025 proved that point very clearly.
If you look closely, many of the failures from 2025 map directly to areas covered by ISO 27001.
The standard addresses:
This is why organizations are now looking beyond tools and asking for auditors and governance experts.
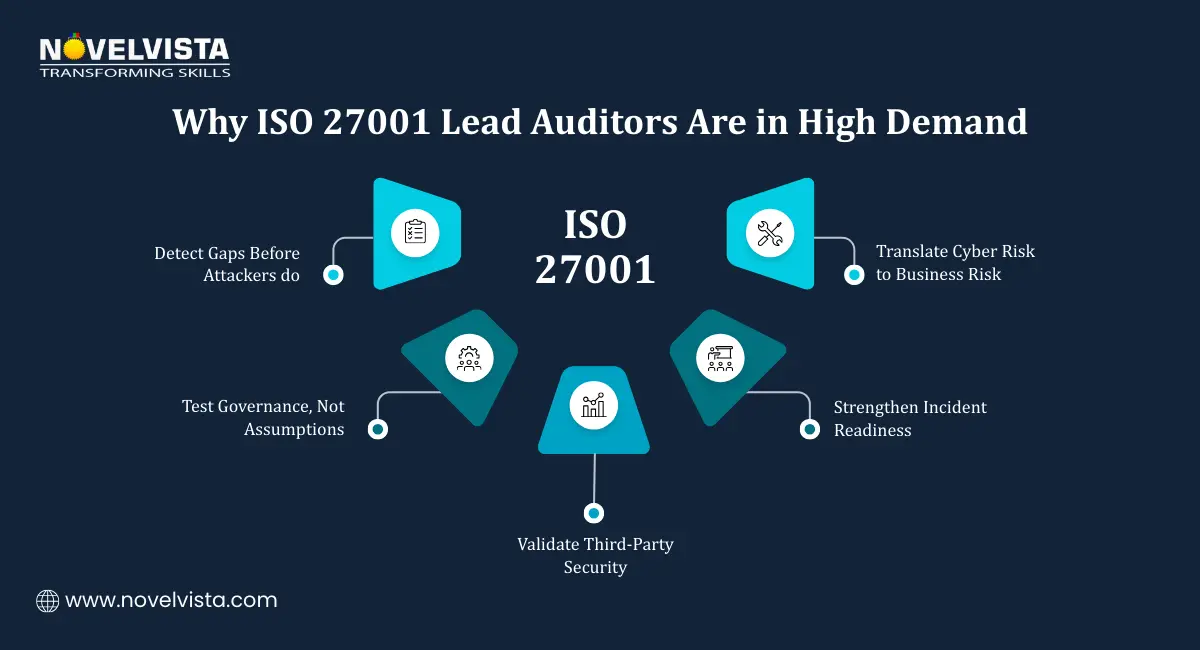
ISO 27001 Lead Auditors don’t just check compliance. They:
In a world where attacks are fast and complex, having someone who can see the whole system is incredibly valuable.
That’s why demand for ISO 27001 Lead Auditors continues to grow — across enterprises, consultancies, regulators, and service providers.
For security professionals watching 2025 unfold, one thing became clear:
reactive security is no longer enough.
NovelVista’s ISO 27001 Lead Auditor Certification Course is designed for professionals who want to move into that next level of responsibility.
It’s built for:
And it focuses on real-world scenarios, not just clauses and definitions.
Professionals learn how to:
This is the skill set organizations are actively looking for right now — especially after the lessons of 2025.
These top cyber attacks of 2025 weren’t random.
They were signals.
They showed that attackers evolve faster than unstructured defenses.
They proved that tools alone can’t compensate for weak governance.
And they reminded us that cyber risk is now business risk.
As we move into 2026, organizations will need more than firewalls and alerts. They will need:
For security professionals, this is a moment of opportunity.
Those who understand ISO 27001 auditing and security governance won’t just respond to incidents — they’ll help prevent them.
2025 was the warning.
What we do next will decide who stays resilient and who doesn’t.
Author Details
Confused About Certification?
Get Free Consultation Call
Stay ahead of the curve by tapping into the latest emerging trends and transforming your subscription into a powerful resource. Maximize every feature, unlock exclusive benefits, and ensure you're always one step ahead in your journey to success.