Category | Other
Last Updated On 03/04/2026
A lot of people want to get into ethical hacking, but do not know where to start. They watch a few tutorials, and then feel completely lost when they realize how much there is to actually learn.
The problem is not motivation. It is the lack of a clear map of Ethical Hacking Skills to build, in what order, and why each one matters.
This guide covers exactly that: the core technical skills, essential tools, 2026 priorities, realistic time investment, and a structured three-stage learning path from beginner to job-ready.
| Topic | Key Point |
| Core skill pillars | Networking, OS proficiency, programming, and tool mastery |
| Essential tools | Nmap, Wireshark, Metasploit, Burp Suite |
| 2026 priorities | Cloud security, AI threats, IoT vulnerabilities, and cryptography basics |
| Time to junior level | 500 to 950 hours, depending on background and learning intensity |
| Learning stages | Fundamentals (200 to 300 hours), tools and phases (3 to 6 months), certify and specialize |
| Top certifications | CEH v13, OSCP, CompTIA PenTest+ |
| Lab platforms | HackTheBox and TryHackMe for hands-on practice |
| Talent gap | Demand for skilled penetration testers is growing faster than supply in 2026 |
The cybersecurity threat landscape has changed significantly. Attacks are more sophisticated. Cloud and IoT attack surfaces have expanded. AI-assisted threats are now a practical reality rather than a future concern.
Organizations know this. Enterprise demand for skilled penetration testers is growing faster than the talent pool can fill it. That gap creates genuine career opportunities for professionals who build the right Ethical Hacking Skills with a structured approach.
2026 is a pivotal year for three reasons:
In our cybersecurity training programs, over 60% of learners initially struggle due to unclear skill sequencing, but structured learning paths reduce dropout rates within the first 4–6 weeks.
This guide is useful whether you are mapping out your learning journey from scratch, identifying gaps in your existing knowledge, or evaluating what it realistically takes to break into offensive security.
To understand what went wrong and how to stay prepared, explore our report on Top 10 Cyber Attacks That Shook 2025: Key Lessons and How to Prepare for 2026.
Before anything else, there are four foundational areas that every practitioner must build. These are the Ethical Hacking Core Skills that everything else sits on top of. Skip any one of them, and you will hit gaps in your practical work that no tool or certification can compensate for.
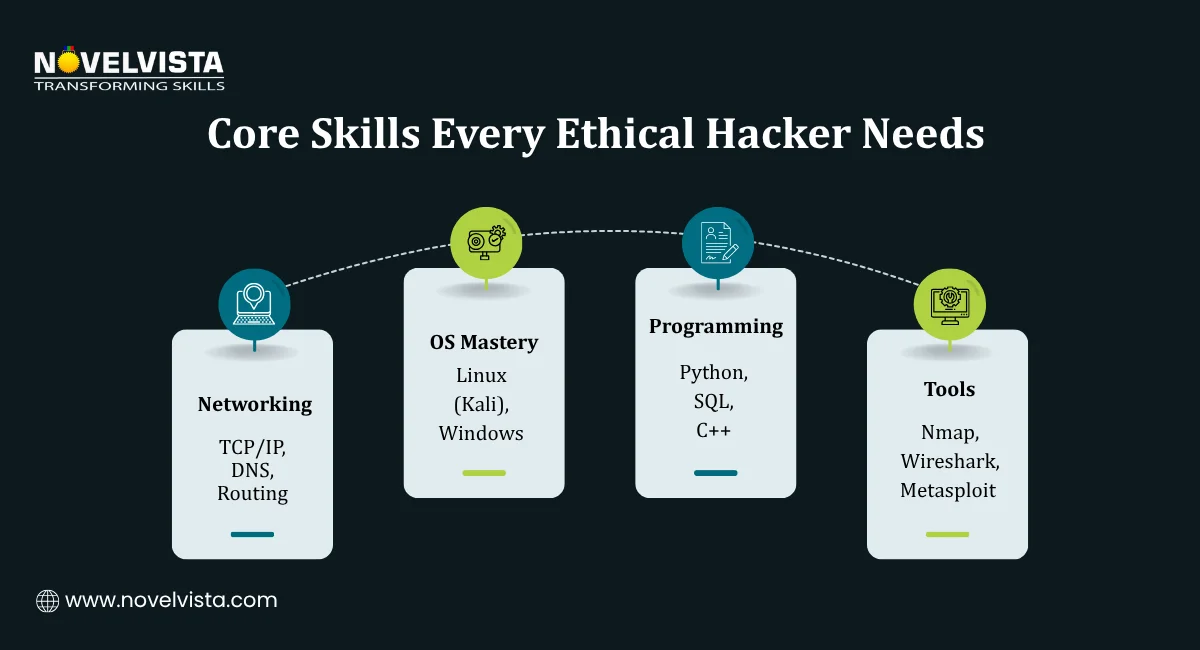
Networking is the language of attack and defense. If you do not understand how traffic moves across systems, you cannot understand how attacks work or how to find vulnerabilities in them.
Key areas to cover:
This knowledge does not need to reach network engineer depth. It needs to reach the level where you can look at a packet capture in Wireshark and understand what you are seeing.
Most penetration testing happens on Linux systems and against Windows targets. You need to be comfortable in both environments.
Specifically:
Kali Linux is the standard platform for ethical hacking work. Getting comfortable in it early is one of the most practical investments a beginner can make.
You do not need to be a software developer to be an effective ethical hacker. But you do need enough programming knowledge to write simple scripts, read exploit code, and understand what an application is doing under the hood.
The most relevant languages for Ethical Hacking Skills development:
In hands-on labs we conduct, learners who build small Python automation scripts early reduce manual testing time by nearly 25% within their first 10 practice scenarios.
Three tools appear more consistently across penetration testing job descriptions than any others:
| Tool | Primary Use |
| Nmap | Network discovery and port scanning during reconnaissance |
| Wireshark | Packet capture and network traffic analysis |
| Metasploit | Exploitation framework for testing and validating vulnerabilities |
Hands-on experience with these three tools is the minimum baseline for any junior penetration testing role. Everything else builds on top of this foundation.
Once the four pillars are in place, the skills needed for ethical hacking can be organized into three categories that work together across a real penetration test.
Understanding where each skill fits within the ethical hacking lifecycle is just as important as the skills themselves:
The reporting phase is one of the most overlooked of all skills needed for ethical hacking. A penetration test that produces findings nobody can act on has not delivered value. Clear, structured technical writing is a professional skill that junior pentesters consistently underinvest in.
The foundational skills above have not changed significantly. What has changed is what needs to sit on top of them. These are the essential skills for ethical hacking that 2026 specifically demands.
XSS (Cross-Site Scripting) and SQL injection remain the most common web vulnerabilities found in penetration tests. Deep proficiency in identifying, exploiting, and documenting these vulnerabilities is non-negotiable for any web application testing role.
Burp Suite is the primary tool here. Comfort with its proxy, scanner, and repeater functions should be part of every practicing ethical hacker's toolkit.
As organizations move workloads to AWS, Azure, and Google Cloud, cloud misconfigurations have become one of the most common sources of real-world breaches. Essential skills for ethical hacking in cloud environments now include:
Cloud security knowledge is moving from a specialist area to a baseline expectation in penetration testing job descriptions. In recent enterprise security audits, over 50% of critical findings are now linked to cloud misconfigurations, reinforcing the shift toward cloud-first security skill requirements.
Two areas that are rapidly becoming standard scope in penetration assessments:
Understanding encryption protocols, hashing algorithms, and certificate management is foundational for assessing secure communications. Ethical Hacking Skills in cryptography do not require deep mathematical knowledge; they require enough practical understanding to identify implementation flaws, weak cipher configurations, and certificate mismanagement.
Two non-technical essential skills for ethical hacking that consistently separate professional pentesters from tool operators:
With 32 or more recognized certifications available in the ethical hacking space, choosing where to focus matters:
CompTIA PenTest+: A structured entry-level credential well-suited to practitioners building toward their first junior role (Check Out the Certification)

This is the question most beginners ask first and get the least honest answer to. So here is a straight answer.
The time required to learn ethical hacking skills to a junior proficiency level is 500 to 950 hours of focused study and practice. That range exists because prior technical background makes a significant difference. Someone coming from a networking or development background will move through the fundamentals faster than someone starting with no technical experience at all.
Learning Stage | Time Investment |
| Networking and OS fundamentals | 4 to 8 weeks of focused study |
| Intermediate skills — exploitation, tool proficiency, hacking phases | 3 to 6 months |
| Advanced labs, certification prep, and specialization | Ongoing beyond the initial 500 to 950 hours |
The time required to learn ethical hacking skills is front-loaded. The fundamentals phase is the slowest and most frustrating part of the journey. Networking concepts, Linux command line proficiency, and basic programming feel abstract when you want to be running exploitation tools.
But this phase directly determines how quickly everything else builds. A practitioner who rushes through fundamentals to get to the interesting tools ends up going back to fill gaps repeatedly, which takes longer overall than building the foundation properly the first time.
A few practical points on managing this time investment:
Lab time counts: Hours spent on HackTheBox or TryHackMe machines are part of your 500 to 950 hours. They are not extra. They are essential.
Follow a structured 3-stage roadmap, master tools like Nmap and Burp Suite,
and build real-world skills through labs, certifications, and hands-on practice.
Knowing what Ethical Hacking Skills to build is one thing. Having a structured path to build them in the right order is another. Here is a practical three-stage roadmap from zero to job-ready.
This stage is about building the foundation that everything else sits on. It is the slowest stage and the most important one.
Networking (4 to 6 weeks)
Study material: CompTIA Network+ curriculum or equivalent covers everything you need at this stage.
Focus areas:
Operating Systems (3 to 5 weeks)
Programming Basics (3 to 4 weeks)
Stage 1 Goal:
By the end of this stage, you should be able to:
Stage 2 is where Ethical Hacking Skills start to feel practical. You are working through real attack scenarios in lab environments and building the hands-on proficiency that employers care about.
Working Through the Hacking Phases
Go through each phase hands-on rather than just reading about them:
Lab Platforms to Use
Two platforms stand out for structured, legal practice environments:
Stage 2 Goal:
Complete at least 20 to 30 lab machines across both platforms before moving to certification. Document your findings for each one. By the end of Stage 2, you should have a portfolio of completed machines and written reports that demonstrate practical Ethical Hacking Skills to a potential employer.
Stage 3 is about converting your practical skills into recognized credentials and beginning to specialize in the area of the market you want to work in.
Choosing the Right Certification
Certification | Best For | Key Characteristic |
| CEH v13 | Broad industry recognition | Now includes AI threat assessment as core content |
| OSCP | Hands-on credibility | Practical exam requiring real exploitation in a lab environment |
| CompTIA PenTest+ | Structured entry-level credential | Good starting point for those building toward their first junior role |
The right choice depends on where you are in the learning journey and which part of the job market you are targeting.
Choosing a Specialization
Once you have a foundational certification, begin developing depth in one area:
Stage 3 Goal:
Hold at least one recognized certification and a documented portfolio of lab work before applying for junior pentesting roles. The combination of credentials and portfolio demonstrates both theoretical knowledge and practical capability, which is what hiring managers in this space actually evaluate.
Training data shows that candidates combining certification with a documented lab portfolio are 40% more likely to secure interview calls for junior penetration testing roles.
Building strong Ethical Hacking Skills in 2026 requires more than downloading tools and watching tutorials. It requires a structured approach that starts with solid fundamentals, builds through hands-on practice, and develops into recognized credentials and practical specialization.
The skills needed for ethical hacking are clearly mapped. Networking, OS proficiency, programming basics, and core tool familiarity form the foundation. Cloud security, AI awareness, IoT knowledge, and strong reporting skills sit on top of that foundation as the 2026 priorities that distinguish competitive candidates from the rest.
The time investment is real; 500 to 950 hours to junior proficiency is a significant commitment. But it is a well-defined and achievable target for anyone with a consistent study habit and a structured plan.
Assess which of the three learning stages you are currently in. Identify the single biggest gap in your Ethical Hacking Skills at that stage. Close that gap before moving to the next one. That focused approach will get you job-ready faster than trying to build everything at once.

NovelVista's Ethical Hacking Professional Certification Training gives you a structured curriculum, hands-on lab practice, and certification preparation to build job-ready Ethical Hacking Skills efficiently. The course covers every stage of the learning path. From networking fundamentals and tool proficiency to advanced exploitation techniques and professional reporting.
Explore NovelVista's Ethical Hacking Professional Certification Training and take the first step toward your cybersecurity career.
Author Details
Confused About Certification?
Get Free Consultation Call
Stay ahead of the curve by tapping into the latest emerging trends and transforming your subscription into a powerful resource. Maximize every feature, unlock exclusive benefits, and ensure you're always one step ahead in your journey to success.