Category | CLOUD and AWS
Last Updated On 19/02/2026
Cybercrime is projected to cost the world over $10 trillion annually, and cloud-based breaches now account for more than 45% of reported enterprise incidents. Despite heavy investments in firewalls and network controls, organizations continue to suffer data leaks, credential theft, and lateral movement attacks.
Why?
Because perimeter-based security is no longer enough.
If you’re a cloud architect, DevOps engineer, CISO, or preparing for the AWS Certified Security Specialty Zero Trust topics, this guide is for you. If you manage workloads in AWS and wonder:
Then understanding Zero Trust Architecture in AWS is no longer optional; it’s foundational.
This blog is your practical, implementation-focused roadmap to building AWS zero trust environments that are resilient, scalable, and future-ready.
At its core, AWS's zero-trust architecture follows a simple principle:
Never trust. Always verify.
Unlike traditional security models that trust internal network traffic, zero trust AWS assumes every request, whether inside or outside the VPC must be authenticated, authorized, and continuously validated.
Zero Trust is built on three pillars:
In the AWS ecosystem, zero-trust architecture AWS integrates identity management, micro-segmentation, continuous monitoring, and encryption to eliminate implicit trust.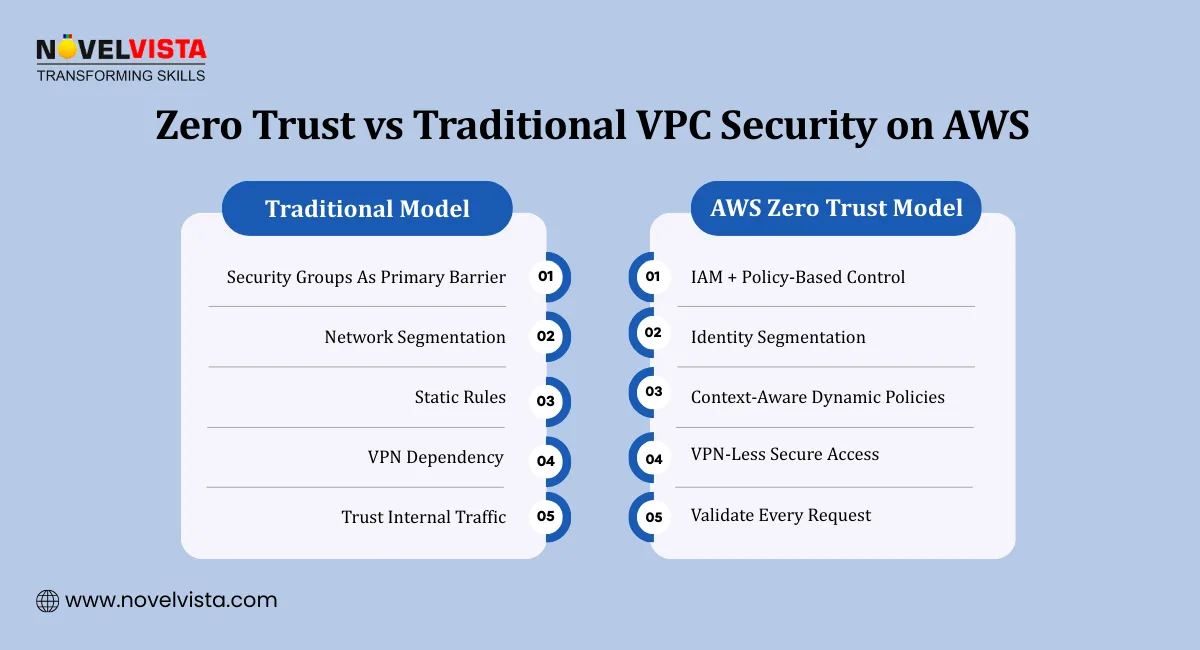
Many teams believe that properly configured VPCs, security groups, and NACLs are sufficient.
But here’s the difference:
| Feature | Traditional VPC Security | Zero Trust Architecture | Primary AWS Service |
| Trust Model | Trust's Internal Network | Verifies Every Request | AWS IAM Identity Center |
| Access Type | Network-Based (VPN) | Identity-Based (ZTA) | AWS Verified Access |
| Enforcement | Static Firewall Rules | Dynamic Policy-Driven | Verified Permissions (Cedar) |
| Connectivity | IP/CIDR-Based | Service-to-Service Auth | Amazon VPC Lattice |
| Authentication | One-Time Validation | Continuous Authentication | AWS CloudTrail |
| Segmentation | Network Segmentation | Micro-Segmentation + Identity | Amazon VPC Lattice |
The problem with perimeter-only defense is lateral movement. Once inside, attackers move freely.
In contrast, AWS zero trust enforces strict identity verification at every layer.
Implementing zero trust architecture AWS requires aligning multiple AWS services.
AWS Identity and Access Management (IAM) forms the foundation. Every user, role, and service must be uniquely identified and authenticated.
Key practices:
Enforce MFA everywhere
Use IAM roles instead of long-term credentials
Implement temporary credentials via STS
Over-permissioned IAM roles are a major risk. Applying least privilege is central to zero trust AWS.
Use:
IAM Access Analyzer
Permission boundaries
SCPs (Service Control Policies)
Continuous authentication means trust is dynamic, not static. In a mature aws zero trust architecture, validation happens continuously — not just at login.
Behavioral Analytics via CloudTrail
Track user and role activity across your AWS environment to detect unusual behavior patterns over time. Continuous log analysis helps identify compromised credentials early.
Context-Aware Policies
Access decisions should adapt based on user location, device type, risk score, and session context. This ensures authorization aligns with real-time conditions, not static assumptions.
Device Posture Validation
Verify that devices meet compliance requirements before granting access to sensitive workloads. Checking OS version, patch level, and security configuration reduces exposure.
Real-Time Anomaly Detection
Implement automated alerting and response mechanisms to detect abnormal API usage or access attempts instantly. Rapid detection limits breach impact and lateral movement.
Deep Visibility with VPC Flow Logs & Traffic Mirroring
You cannot verify what you cannot see. Use VPC Flow Logs to monitor “who is talking to whom,” and leverage Traffic Mirroring for deep packet inspection when Amazon GuardDuty flags suspicious behavior.
Zero Trust is not a one-time authentication event — it is continuous validation embedded into your security architecture.
Amazon VPC Lattice Zero Trust Patterns enable service-to-service authentication and fine-grained policies.
Instead of open network access:
Services authenticate via IAM
Access policies govern communication
Traffic is authorized, not assumed
This reduces blast radius dramatically.
Here is your practical AWS Zero Trust Implementation Guide roadmap.
Centralize identity using AWS IAM Identity Center to unify authentication and authorization across accounts and workloads.
Enforce strong password policies and eliminate long-term access keys wherever possible.
Mandate MFA for all privileged roles and high-risk users to reduce credential compromise risk.
Adopt FIDO2/passkeys and hardware security keys for phishing-resistant authentication aligned with mature aws zero trust architecture practices.
Replace weak authentication mechanisms with hardware-backed factors to prevent man-in-the-middle and credential interception attacks.
Expert Tip: In 2026, SMS-based MFA is no longer considered Zero Trust compliant due to interception and SIM-swap risks. Prioritize phishing-resistant MFA to meet modern zero trust AWS standards.
Audit roles regularly. Remove unused permissions.
Adopt:
Attribute-Based Access Control (ABAC)
Role segmentation per workload
Scoped permissions for services
Traditional VPNs create network-level trust.
With VPN-less access AWS Verified Access, users gain application-level access based on identity and device context.
Benefits:
No open network exposure
Context-aware policy enforcement
Zero implicit trust
This is a critical evolution in zero trust AWS.
Fine-grained authorization with Cedar AWS enables expressive and scalable policy modeling within an aws zero trust architecture. Cedar is the policy language used by AWS Verified Permissions, making it essential for application-level authorization in zero trust AWS environments.
Cedar policies enable:
Attribute-based authorization (ABAC)
Dynamic, real-time policy evaluation
Application-layer access enforcement
Instead of binary access decisions, Cedar supports granular conditions like:
“Allow if user department equals Finance AND device compliance equals true.”
By leveraging AWS Verified Permissions with Cedar, organizations significantly strengthen their zero trust architecture AWS implementation.
Enable:
AWS CloudTrail
GuardDuty
Security Hub
Continuous monitoring ensures your AWS zero-trust model adapts to evolving threats. Follow a structured Roadmap to AWS Certification to build strong cloud fundamentals, master architecture best practices, and confidently pass your AWS exam.
As AI agents and automation increase, identity complexity grows.
Machine Identity: Treat every AI agent as an independent identity within your aws zero trust architecture, not as a shared service account. Assign a unique IAM role per agent to eliminate shared credentials and ensure full traceability.
Scoped Permissions: Enforce strict least-privilege access aligned with zero trust AWS principles. Limit API permissions to the exact scope required so AI agents never inherit broad or wildcard access.
Micro-Segmentation: Isolate agents at the network and service layer using VPC controls or Amazon VPC Lattice Zero Trust Patterns. Ensure agents communicate only with explicitly authorized services within your zero trust architecture AWS model.
Behavioral Guardrails: Implement real-time monitoring and anomaly detection to continuously validate agent activity. In a mature aws zero trust architecture, machine identities are monitored with the same rigor as human users because trust is never permanent.
In AWS zero trust architecture, machine identities are treated with the same rigor as human users.
Using Amazon VPC Lattice Zero Trust Patterns, organizations can enforce IAM-based service authentication, apply policy-driven service communication, and eliminate reliance on IP-based trust within their AWS zero trust architecture. Instead of allowing traffic based on network location, services authenticate through identity and explicit authorization policies. This approach aligns directly with zero trust AWS principles by replacing implicit network trust with verified identity trust, strengthening overall zero trust architecture AWS implementation across distributed workloads.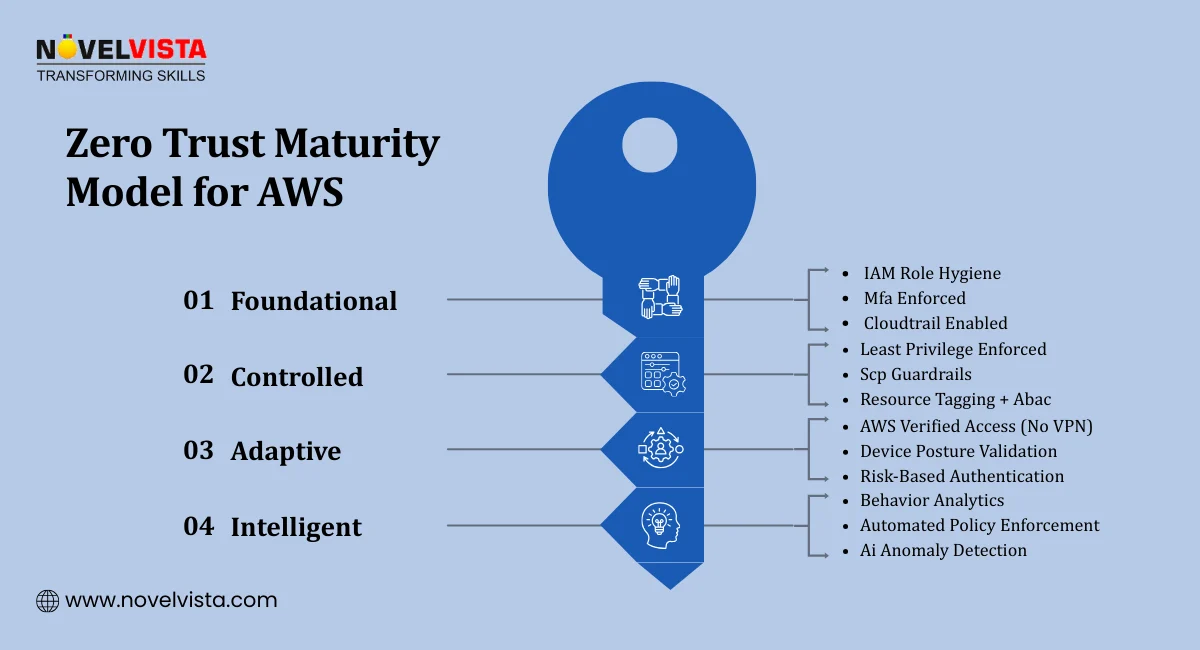
Despite its advantages, zero trust architecture AWS adoption comes with challenges:
Teams are accustomed to network-based trust models.
Fine-grained policies require careful governance.
Older workloads may not support identity-centric controls easily.
However, incremental adoption through an AWS Zero Trust Implementation Guide framework simplifies transition. A comprehensive AWS Certification guide helps you understand exam domains, plan your preparation strategy, and align your skills with real-world cloud architecture requirements.
Cloud adoption is accelerating, AI workloads are expanding, and remote access is now standard. In this reality, perimeter security alone is fragile. Once credentials are compromised, traditional defenses struggle to prevent lateral movement. Zero Trust Architecture in AWS embeds identity verification, least-privilege access, and continuous validation into every layer of your environment. A structured AWS zero trust architecture reduces breach impact, strengthens compliance posture, and future-proofs AI and automation ecosystems.
Organizations implementing mature AWS zero trust models gain stronger visibility and faster incident containment. Ultimately, zero trust architecture AWS is not a product it is a strategic security mindset. And in 2026 and beyond, it will define resilient cloud security.
Ready to design secure, resilient cloud systems with confidence? Join NovelVista’s AWS Solutions Architect – Associate Certification Training and gain practical cloud architecture expertise, real-world security design insights, and industry-recognized credentials. Designed for cloud architects, DevOps engineers, and IT professionals, this course helps you build scalable AWS environments aligned with modern security principles — including identity-driven models and Zero Trust Architecture in AWS.
Take the next step in mastering secure AWS design and advance your cloud career today.
Author Details
Course Related To This blog
AWS Solution Architect Associates
Confused About Certification?
Get Free Consultation Call
Stay ahead of the curve by tapping into the latest emerging trends and transforming your subscription into a powerful resource. Maximize every feature, unlock exclusive benefits, and ensure you're always one step ahead in your journey to success.